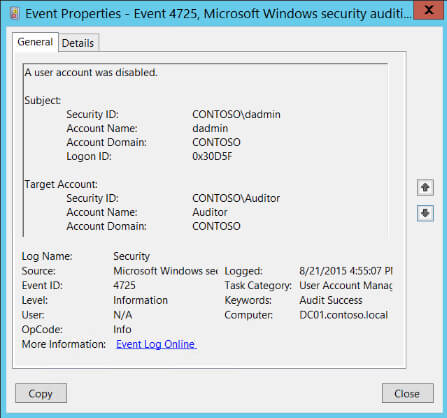
The user identified by Subject: disabled the user identified by Target Account:.
This event is logged both for local SAM accounts and domain accounts.
You will also see event ID4738 informing you of the same information.
Description Fields in
4725
Subject:
The user and logon session that performed the action.
- Security ID: The SID of the account.
- Account Name: The account logon name.
- Account Domain: The domain or — in the case of local accounts — computer name.
- Logon ID is a semi-unique (unique between reboots) number that identifies the logon session. Logon ID allows you to correlate backwards to the logon event (4624) as well as with other events logged during the same logon session.
Target Account:
- Security ID: SID of the account
- Account Name: name of the account
- Account Domain: domain of the account
Stay up-to-date on the Latest in Cybersecurity
Sign up for the Ultimate IT Security newsletter
to hear about the latest webinars, patches, CVEs, attacks, and more.
One of the most challenging tasks Administrators face on a daily basis is managing Active Directory user accounts. It is particularly important to monitor who and why changes are being made to ensure that they are valid.
Why it’s Important to Track Disabled User Accounts in Active Directory
Active Directory configuration changes need to be carefully monitored so that users have access to all the resources they require. If a user’s account becomes disabled, they will not have access to essential system functions including email, files and SharePoint which will disrupt business operations.
Another reason to ensure that disabled users are tracked in Active Directory is to reduce the risk of a data breach. Disabled accounts represent a serious threat as they can be re-enabled and misused by attackers seeking access to Active Directory, Windows servers and other AD-integrated systems. Therefore, it is crucial to have visibility over who disabled a user account to establish the reason for doing this.
In this article, we will discuss the steps you need to take to detect who disabled a user account in Active Directory. We will first look at doing this using native auditing, followed by a more straightforward approach using the Lepide Auditor for Active Directory.
Find Who Disabled a User Account using Event Logs (Event ID 4725)
Please follow the below steps:
- Run gpmc.msc to open the Group Policy Management Console.
- Create a new GPO and Edit it
- Go to Computer Configuration, Policies, Windows Settings, Security Settings, Local Policies > Audit Policy:
- Double click Audit Account Management Policy, Define, Success.
- Click Apply and OK
- Go to Event Log, Define:
- Maximum security log size to 4GB
- Retention method for security log to Overwrite events as needed.
- Link the new GPO to the OU with User Accounts: Go to Group Policy Management, Right-click the defined OU, choose Link an Existing GPO, Choose the GPO that you’ve created.
- Force the group policy update, In Group Policy Management, Right-click the defined OU, Click on Group Policy Update.
- Full Control
- List Contents
- Read all properties
- Read permissions, Click OK.
- Open ADSI Edit, Connect to Default naming context, Right-click DomainDNS object with the name of your domain, Properties, Security (Tab), Advanced (Button), Auditing (Tab), Add Principal Everyone, Type Success, Applies to This object and Descendant objects, Permissions, Select all check boxes except the following:
- Open Event viewer and search Security log for event ID’s 4725 (User Account Management task category).
Note: This event only generates on domain controllers and member servers.
How Lepide Auditor Helps
A quicker and more straightforward way to identify who has disabled a user is to use Lepide Auditor for Active Directory. Our Active Directory auditing software can provide you with in-depth visibility with real-time alerts that help you overcome the limitations of native auditing.
The following is an example of the User Status Modifications report, one of many pre-defined reports included the Lepide Auditor:
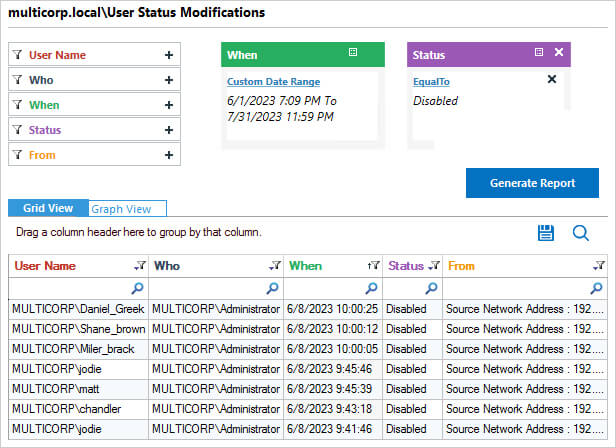
The report includes information showing the User Name of the account which has been disabled together with Who has disabled it.
To run the report:
- From the States & Behavior window, choose Active Directory Reports and select User Status Modifications
- Specify a date range, select Disabled from the Status filter and click Generate Report
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Indicates that a user account was successfully disabled.
Find more information about this event on ultimatewindowssecurity.com. Corresponding events on other OS versions:
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Sample: | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Log Name: Security Source: Microsoft-Windows-Security-Auditing Date: 10/28/2009 8:29:33 PM Event ID: 4725 Task Category: User Account Management Level: Information Keywords: Audit Success User: N/A Computer: dcc1.Logistics.corp Description: A user account was disabled. Subject: Security ID: S-1-5-21-1135140816-2109348461-2107143693-500 Account Name: ALebovsky Account Domain: LOGISTICS Logon ID: 0x2a88a Target Account: Security ID: S-1-5-21-1135140816-2109348461-2107143693-1148 Account Name: wrks12$ Account Domain: LOGISTICS |
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Log Type: | Windows Event Log | |||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Uniquely Identified By: | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
| Field Matching |
|
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
Always fun to try to figure out what is happening on your network or [easyazon_link identifier=”0735666318″ locale=”US” tag=”wn0d5-20″] server [/easyazon_link]. Especially if something happened and no one knows who did it. It is not much fun for user if he cannot login and his or her account has been disabled, either by accident or maliciously. If you setup properly audit in Active Directory it is very easy to find out in event logs who did what and why.
Here are steps how to setup detection of who disabled account in Active Directory on [easyazon_link identifier=”0735682674″ locale=”US” tag=”wn0d5-20″] Windows Server 2012 R2 [/easyazon_link].
- Run gpedit.msc > Create a new GPO > Edit it > Go to “Computer Configuration” > Policies > Windows Settings > Security Settings > Local Policies > Audit Policy:
- Click Audit account management > Define > Success
In next step
- Go to Event Log > Define:
- Maximum security log size 4 GB
- Retention method for security log to Overwrite events as needed
In next step link this created GPO to your USERS OU in Active Directory.
- Force the group policy update > In “Group Policy Management” > Right-click the defined OU > Click on “Group Policy Update“
- Open ADSI Edit > connect to Default naming context > Right-click DomainDNS object with the name of your domain
- Click Properties > Security Tab > Advanced button > Auditing Tab > Permissions > Select all check boxes except the following:
- Full ControlList ContentsRead all propertiesRead permissions > click “OK“
Now you can go to test your new audit policy in Active Directory, go to USERS OU and disable some user account. Open Event viewer and search Security log for event ID 4725 (User Account Management task category). Once you located the event ID you should see the disabled account and your name as the one who disabled the account in [easyazon_link identifier=”1449320023″ locale=”US” tag=”wn0d5-20″] Active Directory [/easyazon_link].
Incase you want to pull all these events from log in PowerShell:
PS C:\>Get-EventLog -LogName Security -Newest 10 | Where-Object { $_.EventID -eq 4725 }
This way you can check if such events happened on your server before you want to see details about the event.
[easyazon_image align=”none” height=”160″ identifier=”0672336227″ locale=”US” src=”http://blog.technotesdesk.com/wp-content/uploads/2015/12/41Wm2-bgH2L._SL160_.jpg” tag=”wn0d5-20″ width=”123″]