Windows Event Forwarding Guidance
About This Repository
Over the past few years, Palantir has a maintained an internal Windows Event Forwarding (WEF) pipeline for generating and centrally collecting logs of forensic and security value from Microsoft Windows hosts. Once these events are collected and indexed, alerting and detection strategies (ADS) can be constructed not only on high-fidelity security events (e.g. log deletion), but also for deviations from normalcy, such as unusual service account access, access to sensitive filesystem or registry locations, or installation of malware persistence.
The goal of this project is to provide the necessary building blocks for organizations to rapidly evaluate and deploy WEF to a production environment, and centralize public efforts to improve WEF subscriptions and encourage adoption. While WEF has become more popular in recent years, it is still dramatically underrepresented in the community, and it is our hope that this project may encourage others to adopt it for incident detection and response purposes. We acknowledge the efforts that Microsoft, IAD, and other contributors have made to this space and wish to thank them for providing many of the subscriptions, ideas, and techniques that will be covered in this post.
About Windows Event Forwarding
Windows Event Forwarding (WEF) is a powerful log forwarding solution integrated within modern versions of Microsoft Windows. One of the most comprehensive descriptions of WEF can be found on the Microsoft Docs page here, but is summarized as follows:
- Windows Event Forwarding allows for event logs to be sent, either via a push or pull mechanism, to one or more centralized Windows Event Collector (WEC) servers.
- WEF is agent-free, and relies on native components integrated into the operating system. WEF is supported for both workstation and server builds of Windows.
- WEF supports mutual authentication and encryption through Kerberos (in a domain), or can be extended through the usage of TLS (additional authentication or for non-domain joined machines).
- WEF has a rich XML-based language that can control which event IDs are submitted, suppress noisy events, batch events together, and send events as quickly or slowly as desired. Subscription XML supports a subset of XPath, which simplifies the process of writing expressions to select the events you’re interested in.
Repository Layout
This repository is organized as follows:
- WEF Subscriptions: Subscriptions are the core component of WEF that determine which events should be forwarded, how they should be stored, and at what cadence and batch size they are sent.
- Windows Event Channels: Event Channels are queues that can be used for collecting and storing event log entries on a collector server.
- Group Policy Objects: GPO recommendations for configuring auditing, enabling windows event collection/forwarding, etc.
- AutorunsToWinEventLog: A script leveraging existing WEF infrastructure and Sysinternals’ Autoruns to collect persistence and auto-start related artifacts.
Using This Repository
Note: We recommend that you spin up a lab environment before deploying any of these configurations, scripts, or subscriptions to a production environment.
- Download the repository and review the contents.
- Deploy auditing GPOs to your fleet to start collecting security-critical events.
- Configure one or more Windows Event Collector servers. Apply the associated GPOs.
- (Optional) Configure your WEC server(s) to function as a powershell transcription logging target.
- Deploy the windows event channels to the WEC server(s).
- Load one or more WEF subscriptions on the WEC server(s).
- Start collecting data and hunting badness.
Contributing
Contributions, fixes, and improvements can be submitted directly against this project as a GitHub issue or pull request. When contributing an update to CustomEventChannels.man, please do not include the compiled .DLL for security reasons. Once your pull request has been merged, we will compile the updated manifest into a DLL and add it to the repository.
License
MIT License
Copyright (c) 2018 Palantir Technologies Inc.
Permission is hereby granted, free of charge, to any person obtaining a copy
of this software and associated documentation files (the «Software»), to deal
in the Software without restriction, including without limitation the rights
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
copies of the Software, and to permit persons to whom the Software is
furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all
copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED «AS IS», WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
SOFTWARE.
Further Reading and Acknowledgements
Many open source publications were referenced for the development of these Subscriptions, and we wish to acknowledge those who have contributed to this effort.
- Palantir Medium: Windows Event Forwarding for Network Defense
- Microsoft Windows Event Forwarding to help with intrusion detection
- Monitoring What Matters
- Spotting the Adversary
- Creating Custom Windows Event Forwarding Logs
- Windows Logging Cheat Sheet
- Event Forwarding Guidance
- Windows Event Log Reference:
- Windows Event Log Consuming Events
- Advanced XML Filtering
- XPath Documentation
- Exploit Guard Event Views
Windows Event Forwarding (WEF) is a built-in feature that allows you to collect logs from multiple Windows machines and centralize them on a single collector system. It’s perfect for monitoring, auditing, security analysis, and compliance.
Instead of logging into each machine and browsing Event Viewer (which, let’s face it, no one enjoys), WEF sends logs over the network to a collector computer, letting you analyze everything in one place.
Whether you’re a sysadmin, SOC analyst, or just someone trying to tame the chaos of logs—this guide is for you.
🧱 Requirements
| ✅ Required Element | 💡 Description |
|---|---|
| Collector Machine | Central system to gather logs |
| Source Computers | Systems that forward events |
| Windows Firewall Config | Must allow WEF traffic |
| Administrative Privileges | Required for setup |
| Group Policy | For automatic configuration (recommended) |
🛠️ Step-by-Step: Configure Windows Event Forwarding
🔧 Step 1: Set Up the Collector Computer
On the machine that will receive events:
- Open Event Viewer (
eventvwr.msc) - In the left panel, right-click Subscriptions > Create Subscription
- Name your subscription (e.g., “Security Events from Clients”)
- Choose Collector Initiated or Source Initiated:
| Type | Use When |
|---|---|
| Collector Initiated | You control which computers to pull from 🧲 |
| Source Initiated | Remote systems push logs automatically 📤 |
- Click Select Computers to add clients
- Choose which events to collect (e.g., Application, System, Security)
- Click Advanced > Minimize Latency for real-time-ish results
- Click OK to save the subscription
📦 You’ve now created the channel for collecting logs!
🧭 Step 2: Configure the Source Computers
There are two ways to do this:
– Automatically via Group Policy (preferred for domain environments)
– Manually for standalone or test systems
🏢 Method A: Configure with Group Policy
- Open Group Policy Management Console (
gpmc.msc) - Create or edit a GPO linked to the OU with source computers
- Go to:
Computer Configuration > Policies > Administrative Templates > Windows Components > Event Forwarding - Enable Configure Target Subscription Manager
- Set the server (collector) using this format:
Server=http://COLLECTOR-HOST:5985/wsman/SubscriptionManager/WEC,Refresh=60 - Apply and force the GPO with
gpupdate /force
💡 If you have DNS, use the hostname instead of IP.
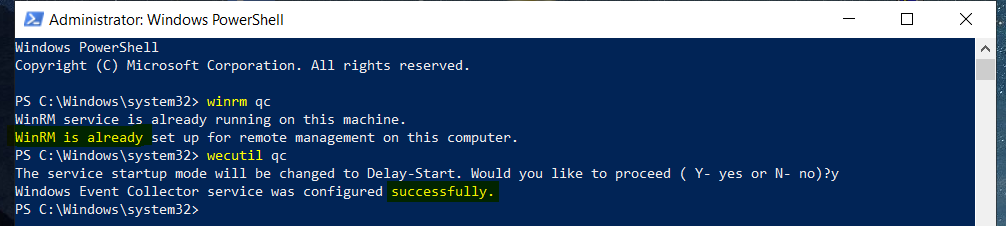
🧪 Method B: Configure Manually (Testing or Small Setups)
Run this on each source computer (with admin rights):
wecutil qc
winrm quickconfig
Then register the subscription manager:
winrm set winrm/config/client @{TrustedHosts="COLLECTOR-HOST"}
And finally:
eventcreate /T INFORMATION /ID 100 /L Application /D "Test WEF Log"
Watch for this on the collector machine.
🧪 Validate the Setup
On the Collector:
- Open Event Viewer
- Navigate to Forwarded Events
- Check for logs from source machines
On the Source Machine:
- Run
gpresult /rto ensure GPO applied - Run
Get-WinEvent -LogName ForwardedEventsto confirm logs are sending
🔒 Tips for Secure WEF Setup
| Tip | Why It Matters |
|---|---|
| Use HTTPS/SSL | Encrypts log traffic (default is HTTP) |
| Filter sensitive event logs | Avoids flooding the collector |
| Use Least Privilege | Don’t use domain admin accounts unnecessarily |
| Monitor Collector Health | Set alerts if it stops receiving logs 🧠 |
🧰 Useful Commands
| Command | Purpose |
|---|---|
wecutil qc |
Quick config on collector |
wecutil es <subscription.xml> |
Import a subscription |
winrm quickconfig |
Set up WinRM for log transport |
Get-WinEvent -LogName ForwardedEvents |
Check logs programmatically |
🧠 Why Use WEF?
| Use Case | How WEF Helps |
|---|---|
| Security Monitoring | Collects logs for SIEMs like Splunk/Sentinel |
| Audit Compliance | Tracks access and system changes |
| Troubleshooting | Centralized event access = faster resolution |
| Resource Efficiency | Avoids installing log agents everywhere |
✅ Summary Table
| Component | Role |
|---|---|
| Collector Computer | Gathers logs |
| Source Computers | Send logs to collector |
| Group Policy | Automates source setup |
| WinRM/WEC | Transports logs securely |
🧭 Final Thoughts
Windows Event Forwarding is one of the most underrated tools in the Windows ecosystem. It’s lightweight, native, and powerful—especially when paired with a SIEM or centralized dashboard.
If you’re managing more than one Windows device, setting up WEF is absolutely worth the effort.
Just don’t forget to monitor the collector—and make sure it’s actually receiving logs. Because a silent collector is worse than a chatty one. 😉
Introduction:
In summary:
- Windows Event Forwarding allows for event logs to be sent, either via a push or pull mechanism, to one or more centralized Windows Event Collector (WEC) servers.
- WEF is agent-free, and relies on native components integrated into the operating system. WEF is supported for both workstation and server builds of Windows.
- WEF supports mutual authentication and encryption through Kerberos (in a domain), or can be extended through the usage of TLS (additional authentication or for non-domain-joined machines).
- WEF has a rich XML-based language to control which event IDs are submitted, suppress noisy events, batch events together, and configure submission frequency. Subscription XML supports a subset of XPath, which simplifies the process of writing expressions to select the events you’re interested in.
A WEF connection requires a few basic components:
- Group Policy Objects (GPOs) to control security auditing and event logging.
- One or more servers with a configured Windows Event Log Collector service (often referred to as the “WEF Server” or “WEF Collector”).
- Functional Kerberos for all endpoints (domain) or a valid TLS certificate (non-domain) for the Event Log Collector servers.
- Windows Remote Management (WinRM) enabled on all workstations and servers that will forward events.
- Firewall rules permitting WinRM connectivity between the devices.
- GPOs to specify the URL of the WEF subscription manager(s).
- One or more event log subscriptions. A subscription is a collection of events based on Event IDs or other criteria to tell the endpoints which event logs to forward.
The following actions occur upon first receiving appropriate GPOs on a workstation:
- The workstation configures security auditing and starts writing to the local event log.
- The workstation connects to the subscription manager(s) using WinRM, authenticated either via Kerberos or TLS. In both cases, transport-layer encryption is applied.
- The workstation registers itself in the registry of the Event Log Collector, and downloads a list of all relevant WEF Subscriptions.
- The workstation periodically sends events to the Event Log Collector(s) as defined in the subscription files. Additionally, the workstation connects on a periodic heartbeat.
As new devices are added to the domain and receive the appropriate security logging and WEF subscription GPOs, they will automatically begin forwarding events, reducing the administrative burden of ensuring log coverage and quality.
Event forwarding (also called SUBSCRIPTIONS) is a mean to send Windows event log entries from source computers to a collector. A same computer can be a collector or a source.
There are two methods available to complete this challenge – collector initiated (also called PULL) and source initiated (also called PUSH):
| Parameter | Collector Initiated (PULL) | Source Initiated (PUSH) |
|---|---|---|
| Socket direction (for firewall rules) | Collector –> Source | Collector –> Source |
| Initiating machine | Collector | Source |
| Authentication Type | Kerberos | Kerberos / Certificates |
This technology uses WinRM (HTTP protocol on port TCP 5985 with WinRM 2.0) . Be careful with the Window firewall and configure it to allow WinRM incoming requests.
WinRM is the ‘server’ component and WinRS is the ‘client’ that can remotely manage the machine with WinRM configured.
Differences you should be aware of:
WinRM 1.1 (obsolete)
Vista and Server 2008
Port 80 for HTTP and Port 443 for HTTPS
WinRM 2.0
Windows 7 and Server 2008 R2, 2012 R2, windows 10, Server 2016 …
Port 5985 for HTTP and Port 5986 for HTTPS
Tool:
https://www.logbinder.com/
Reference articles for WEF and Event forwarding:
Deploying WinRM using Group Policy: http://www.vkernel.ro/blog/how-to-enable-winrm-http-via-group-policy
Microsoft official document well documented:
https://docs.microsoft.com/en-us/windows/threat-protection/use-windows-event-forwarding-to-assist-in-instrusion-detection
https://www.jpcert.or.jp/english/pub/sr/ir_research.html
https://hackernoon.com/the-windows-event-forwarding-survival-guide-2010db7a68c4
http://blogs.technet.com/b/jepayne/archive/2015/11/24/monitoring-what-matters-windows-event-forwarding-for-everyone-even-if-you-already-have-a-siem.aspx
Fresh How-to from Intrusion detection perspective:
https://medium.com/@palantir/windows-event-forwarding-for-network-defense-cb208d5ff86f
How-to easy to follow from Intrusion detection perspective:
https://www.root9b.com/sites/default/files/whitepapers/R9B_blog_005_whitepaper_01.pdf
https://joshuadlewis.blogspot.fr/2014/10/advanced-threat-detection-with-sysmon_74.html
Basic configuration:
on source computers and collector computer: winrm quickconfig and add the collector computer account to the local administrators group
To verify a listener has been created type winrm enumerate winrm/config/listener

Just to round off this quick introduction to WinRM, to delete a listener use winrm delete winrm/config/listener?address=*+Transport=HTTP
on collector computer: wecutil qc. Add the computer account of the collector computer to the Event Log Readers Group on each of the source computers
on collector computer: create a new subscription from event viewer (follow the wizard)
WinRS: WinRS (Windows Remote Shell) is the client that connects to a WinRM configured machine (as seen in the first part of this post). WinRS is pretty handy, you’ve probably used PSTools or SC for similar things in the past. Here are a few examples of what you do.
Connecting to a remote shell
winrs -r:http://hostnameofclient "cmd"
Stop / Starting remote service
winrs -r:http://hostnameofclient "net start/stop spooler"
Do a Dir on the C drive
winrs -r:http://hostnameofclient "dir c:\"

Forwarded Event Logs:
This is configured using ‘subscribers’, which connect to WinRM enabled machines.
To configure these subscribers head over to event viewer, right click on forwarded events and select properties. Select the 2nd tab along subscriptions and press create.
This is where you’ll select the WinRM enabled machine and choose which events you would like forwarded.

Right click the subscription and select show runtime status.

Now it took me a minute or two to figure this one out. Was it a firewall issue (this gives the same error code), did I miss some configuration steps? Well no, it was something a lot more basic than that. Remember earlier on we were talking about the port changes in WinRM 1.1 to 2.0?
That’s right, I was using server 2008 R2 to set the subscriptions which automatically sets the port to 5985. The client I configured initially was server 2008 so uses version 1.1. If you right click the subscription and click properties -> advanced you’ll be able to see this. I changed this to port 80 and checked the runtime status again.
[DC2.domain.local] – Error – Last retry time: 03/02/2011 20:20:30. Code (0x5): Access is denied. Next retry time: 03/02/2011 20:25:30.”
Head back to the advanced settings and change the user account from machine account to a user with administrative rights. After making these changes the forwarded events started to flow.

Additional considerations:
In a workgroup environment, you can follow the same basic procedure described above to configure computers to forward and collect events. However, there are some additional steps and considerations for workgroups:
- You can only use Normal mode (Pull) subscriptions
- You must add a Windows Firewall exception for Remote Event Log Management on each source computer.
- You must add an account with administrator privileges to the Event Log Readers group on each source computer. You must specify this account in the Configure Advanced Subscription Settings dialog when creating a subscription on the collector computer.
- Type
winrm set winrm/config/client @{TrustedHosts="<sources>"}at a command prompt on the collector computer to allow all of the source computers to use NTLM authentication when communicating with WinRM on the collector computer. Run this command only once. Where<sources>appears in the command, substitute a list of the names of all of the participating source computers in the workgroup. Separate the names by commas. Alternatively, you can use wildcards to match the names of all the source computers. For example, if you want to configure a set of source computers, each with a name that begins with “msft”, you could type this commandwinrm set winrm/config/client @{TrustedHosts="msft*"}on the collector computer. To learn more about this command, typewinrm help config.
If you configure a subscription to use the HTTPS protocol by using the HTTPS option in Advanced Subscription Settings , you must also set corresponding Windows Firewall exceptions for port 443. For a subscription that uses Normal (PULL mode) delivery optimization, you must set the exception only on the source computers. For a subscription that uses either Minimize Bandwidth or Minimize Latency (PUSH mode) delivery optimizations, you must set the exception on both the source and collector computers.
If you intend to specify a user account by using the Specific User option in Advanced Subscription Settings when creating the subscription, you must ensure that account is a member of the local Administrators group on each of the source computers in step 4 instead of adding the machine account of the collector computer. Alternatively, you can use the Windows Event Log command-line utility to grant an account access to individual logs. To learn more about this command-line utility, type wevtutil sl -? at a command prompt.
Video:
Tutorials:
1st: Event forwarding between computers in a Domain
http://tutorial.programming4.us/windows_7/Forwarding-Events-(part-1)—How-to-Configure-Event-Forwarding-in-AD-DS-Domains.aspx
2nd: Event forwarding between computers in workgroup
http://tutorial.programming4.us/windows_7/Forwarding-Events-(part-2)—How-to-Troubleshoot-Event-Forwarding—How-to-Configure-Event-Forwarding-in-Workgroup-Environments.aspx
Additional article talking about Event forwarding too:
http://joshuadlewis.blogspot.fr/2014/10/advanced-threat-detection-with-sysmon_74.html
Did you know that Windows has had a built-in capability to function as a SIEM (Security Information and Event Management) system for years, provided you stay within the Windows ecosystem? This powerful feature, known as Windows Event Forwarding (WEF), allows you to centralize event logs from multiple Windows machines, giving you a comprehensive view of your network’s activities.
Today, we’re going to delve into how to use and set up Windows Event Forwarding to get an inventory going on NTLM v1 traffic. By configuring WEF, you can monitor and analyze all kinds if events, helping you detect and address potential security issues in real-time.
Introduction
Windows Event Forwarding (WEF) is a built-in feature available in Microsoft Windows operating systems designed to help organizations manage and analyze event logs in a structured and efficient manner. With WEF, system administrators can centralize event logs from multiple Windows computers and forward them to a central server, providing a consolidated overview of what is happening on those computers.
This functionality is particularly valuable for security and monitoring purposes because it allows organizations to track events in real-time, detect suspicious activities, and quickly identify security incidents. By using WEF, organizations can also reduce the amount of data traffic needed to retrieve event logs from multiple sources, thereby decreasing network load and improving efficiency.
This guide will show the steps on how Windows Event Forwarding should be configured, managed, and used to gain insights from the event logs of Windows computers connected to a domain, with a specific focus on the inventory of NTLMv1. Understanding and correctly implementing WEF can be an important step in improving the security and management of any IT infrastructure.
Architecture overview
The architecture for Windows Event Forwarding (WEF) in this document is based on a domain network where various components play critical roles in effectively managing and analyzing event log data.
- Domain Controllers: Domain controllers play a crucial role in handling authentication and enforcing configuration settings on all computers and devices within the domain. They ensure that event logs are correctly generated and logged by the endpoints.
- Log collectors: Log collectors are responsible for gathering event log data from endpoints, both clients, and servers, within the domain. These log collectors act as central storage points for log data, enabling consolidated analysis and monitoring.
- Endpoints (clients and servers): All machines within the domain are configured to forward event log data to the log collectors. These endpoints are essential for capturing relevant events and forwarding them to the central collection points.
It is important to note that machines outside the domain network are out of the scope of this blog, I’ll write about that feature in the near future. External machines perform their authentication against the domain controllers and servers within the domain where events are captured and logged. For the inventory of NTLMv1 authentication, there is less emphasis on these external machines since most relevant authentication events occur within the internal domain network and can be intercepted accordingly.

Requirements
Before Windows Event Forwarding (WEF) can be used, certain requirements must be met. These ensure smooth implementation without limitations.
- Windows version and edition: Ensure that both the source computers and the destination computer where you want to centralize event logs are running Windows operating systems that support WEF. WEF is available in Windows Vista and later versions, including Windows Server operating systems. It is recommended to use the latest version of Windows Server (Windows Server 2019+).
- Network connectivity: Ensure that all involved computers can communicate within the network. Necessary firewall rules must be configured to ensure that event logs can be safely forwarded to the central server. Using secure communication with Kerberos is strongly recommended to ensure the confidentiality and integrity of log data. Network traffic uses WSMAN port 5985.
- Rights and permissions: To set up and manage WEF, you need administrative rights on both the source computers and the target server. No domain admin rights are needed other than configuring the group policy objects.
- Log source configuration: Carefully configure the event logs on the source computers. You need to determine which events you want to collect and forward to the central server. This includes enabling the correct log channels and filtering events based on their relevance to your monitoring and security purposes.
Hardware requirements
The hardware requirements for a single log collector can vary depending on several factors, such as the volume of log data you want to collect, the frequency of events, and the complexity of your analysis needs. Generally, the more data you collect and analyze, the more powerful the hardware needs to be. Here are some general recommendations for the hardware requirements of a log collector:
- Processor (CPU): A multi-core processor with good processing speed is important for efficiently processing event logs. The exact requirements vary, but a modern quad-core processor or better is recommended. The processor should have a minimum of 4 cores.
- Memory (RAM): The amount of RAM depends on the volume of log data and the complexity of your analyses. Generally, at least 16 GB of RAM is recommended.
- Storage: Sufficient storage space is needed to store log data before it is forwarded to a central location. The required storage space depends heavily on the amount of data you collect and how long you want to retain it. Due to the high level of I/O used for writing the data, a fast and reliable storage solution, such as an SSD, is recommended for optimal performance. A minimum storage disk of 80GB is also recommended for the OS Disk.
- Network Interface: A fast network connection is essential, especially if you are collecting log data from multiple sources. A gigabit Ethernet connection is minimally recommended.
Collector requirements
The log collector has the capacity to receive data from a maximum of 4000 clients. This means that up to 4000 Windows computers or devices can forward their event logs to this collector for further analysis and storage. It is important to keep this maximum number in mind when planning the implementation to ensure it meets the needs of your organization. If you plan to collect data from more than 4000 clients, consider deploying multiple collectors to distribute the load and maintain optimal performance.
Performance updates
For users of Windows Server 2016 and Windows Server 2019, specific updates are available that offer performance improvements for the use of Windows Event Forwarding (WEF). These updates, KB4537806 for Windows Server 2016 and KB4537818 for Windows Server 2019, are designed to enhance the overall performance and efficiency of WEF.
It is important to note that these updates are typically installed as part of regular Windows updates, provided optional updates are enabled. Given that they can offer significant improvements for WEF implementations, they are highly recommended for organizations deploying WEF to collect and manage event logs.
- Windows Server 2016: KB4537806
- Windows Server 2019: KB4537818
Windows event collector setup
The Windows Event Collector (WEC) is a crucial component for the centralized inventory of event logs. It acts as the central collection point for event logs within the domain network and is responsible for receiving and storing log data from endpoints such as clients and servers. Here are the steps to configure it.
Windows Remote Management (WinRM – WSMAN)
Windows Remote Management (WinRM) is a Microsoft service that enables remote communication and management of Windows systems over a network. It allows administrators to execute commands, change configurations, and retrieve data from remote computers running Windows operating systems. With WinRM, administrators can manage system resources and retrieve data from multiple Windows machines without physically accessing each individual computer, which is useful for tasks such as configuration management, troubleshooting, and automation. WinRM is an essential component in using WEF. The following actions are necessary on the WEF collectors.
Note! Windows Server 2008R2 and higher have WinRM enabled by default. The steps below are necessary to ensure this configuration.
WinRM listener
Command-line:
winrm enumerate winrm/config/listenerExpected output:

To view the complete configuration, use the command-line:
Windows firewall
Run the following command-line in an elevated PowerShell console:
Get-NetFirewallRule | Where-Object {$_.Displayname -Like "Windows Remote Management (HTTP-In)" -and $_.Profile -like "*Domain*"} | Select EnabledExpected output:

Windows Remote Management service
Run the following command-line in an elevated PowerShell console:
Get-Service -Name WINRM | select StartTypeExpected output:

Corrective action
If any of the above measures do not produce the desired effect, the following cmdlet can be executed to configure the log collector for using Windows Remote Management:
WinRM collector adjustments for Server 2016/2019
On the collector, both the Windows Event Collector service (WecSvc) and the Windows Remote Management service (WinRM) use certain URLs. However, the default access control lists (ACLs) for these URLs only allow access for the svchost process that runs WinRM. In the default configuration of Windows Server 2016, both WinRM and WecSvc run in a single svchost process. Because this process has access, both services function correctly. However, if you change the configuration so that the services run in separate host processes, WecSvc no longer has access, and event forwarding stops working.
The services function differently in Windows Server 2019. If a Windows Server 2019 computer has more than 3,5 GB of RAM, WinRM and WecSvc run in separate svchost processes by default. Due to this change, event forwarding may also not work correctly in the default configuration.
To correct this oversight, run the following commands in an elevated command console:
netsh http delete urlacl url=http://+:5985/wsman/
netsh http add urlacl url=http://+:5985/wsman/ sddl=D:(A;;GX;;;S-1-5-80-569256582-2953403351-2909559716-1301513147-412116970)(A;;GX;;;S-1-5-80-4059739203-877974739-1245631912-527174227-2996563517)
netsh http delete urlacl url=https://+:5986/wsman/
netsh http add urlacl url=https://+:5986/wsman/ sddl=D:(A;;GX;;;S-1-5-80-569256582-2953403351-2909559716-1301513147-412116970)(A;;GX;;;S-1-5-80-4059739203-877974739-1245631912-527174227-2996563517)Note! When you have upgraded to Server 2022 from 2016 or 2019 you should also take the steps described here.
Note! This correction does not apply to a new installation of Windows Server 2022.
Restart the server or service after making the changes. To view the current configuration, use the command-line:
Source: https://learn.microsoft.com/en-us/troubleshoot/windows-server/admin-development/events-not-forwarded-by-windows-server-collector
Setting up a Windows Event Forwarding (WEF) subscription
A WEF subscription is used to collect specific events from source computers within the domain and forward them to the Windows Event Collector (WEC) for centralized storage and analysis. Here are the steps to set up a WEF subscription:
On the log collector server, open the event viewer and navigate to “Subscriptions”. Click “Yes” when you receive the following prompt.
Right-click on “Subscriptions” and select “Create Subscription”.
In the dialog box, give the subscription a name and select: “Source computer initiated” then click on “Select Computer Groups…”.

Click on “Add Domain Computers” and add the computer group that needs to forward events. It is advisable to select “Domain Computers” here. Machines will then have the ability to forward events but will need further configuration.

Note! When targeting Domain Controllers, select the group “Domain Controllers” as these are not a part of “Domain Computers”.
Click “OK” in this dialog box. Click “Advanced” at the bottom of the screen and select the option “Minimize Latency”. Click “OK”. These options are available:
- “Normal” pull delivery every 15 minutes.
- “Minimize Bandwidth” push delivery every 6 hours.
- “Minimize Latency” for critical events push delivery every 30 seconds.
Note! The “HTTP” protocol is secured by Kerberos encryption.
In the “Select Events” dialog box, specify the event configuration. This can be done in the UI section or via an XPATH (XML tab). Since detecting NTLMv1 is outside the scope of the UI, the following configuration via an XPath filter is recommended:
<QueryList>
<Query Id="0" Path="Security">
<Select Path="Security">*[System[(EventID=4624)]] and Event[EventData[Data[@Name='LmPackageName'] and (Data='NTLM V1' or Data='LM')]] </Select>
<Suppress Path="Security">*[EventData[Data[@Name='TargetUserName'] and (Data='ANONYMOUS LOGON')]]</Suppress>
</Query>
</QueryList>Note! When Windows does not detect NTLMv2 authentication, it assumes NTLMv1 is being used even when an “Anonymous Logon” occurs. This can create the impression that NTLMv1 authentication is taking place despite enforced policies. To filter this out, the “Suppress” option is added as shown above. For more information, see Microsoft’s documentation.
Click “OK” twice to return to the subscription. It will now be configured according to the set conditions. The following will be representative of this setup.

Event log size
Adjusting the size of the “Forwarded Events” log is important to ensure there is enough space to store log data. Here’s the command-line to set the event log size to 1 gigabyte:
wevtutil sl forwardedevents /ms:1000000000Log archiving
Log archiving is an important part of event log management. When an event log is full and can no longer contain data, archiving can be enabled to store older events before new data is recorded. This ensures important log data is preserved for further analysis even when the log is full. Enabling this feature ensures no valuable data is lost. Here is the command-line to enable archiving:
wevtutil sl forwardedevents /ab:true /rt:trueWEF configuration via a Group Policy object (GPO)
A Group Policy Object (GPO) is the way to manage the Windows Event Forwarding (WEF) configuration on multiple computers within the domain. Here are the steps to create a WEF configuration via a GPO:
In “Group Policy Management,” create a group policy object in the organizational unit where the machines that need to receive the WEF configuration are located. This GPO can be filtered based on computer names or a specific group.
Note! Assigning a group to a computer object requires a reboot of the respective host.
Hint! This policy exclusively uses computer configuration, therefore set the GPO Status to: “User configuration settings disabled.”
In the policy, navigate to:Computer Configuration -> Policies -> Windows Settings -> Security Settings -> Restricted Groups
Add a group named “Event Log Readers” and click “OK”.
In “Member of this group,” click “Add” and add the pseudo group “NT AUTHORITY\Network Service.” Click “OK” twice to return.
Note! The above must be done to give the “Network Service” rights to read and forward event logs to the collector.
In the policy, navigate to:Computer Configuration -> Policies -> Windows Settings -> Security Settings -> System Services
Configure the “Windows Remote Management” service to start automatically. Click “OK” to return.

In the policy, navigate to:Computer Configuration -> Policies -> Administrative Templates -> Windows Components -> Event Forwarding
Set the following policies:
- Configure forwarder resource usage: Enabled
- The maximum forwarding rate: 500
- Configure target Subscription Manager: Enabled
Server=http://<FQDN of the collector>:5985/wsman/SubscriptionManager/WEC,Refresh=120
Note! The maximum forwarding rate indicates how many log entries a host can forward at a time. A typical deployment will be between 500 and 1000 entries.
Note! The specified refresh interval is for retrieving the WEF configuration from the subscription. When there are few or no changes, this value can be increased.
In the policy, navigate to:Computer Configuration -> Policies -> Administrative Templates -> Windows Components -> Event Log Service -> Security
Set the following policy:
- Configure Log Access: Enabled
- Log Access:
O:BAG:SYD:(A;;0xf0005;;;SY)(A;;0x5;;;BA)(A;;0x1;;;S-1-5-32-573)(A;;0x1;;;S-1-5-20)Note! In many blogs, S-1-5-20 is replaced by “NS”. This does not work on a Domain Controller; hence, the SID is used in this rule.
Checking the WEF configuration
Once the previously shown configuration is successfully implemented, the log collector configured, and the policies applied to the hosts that need to forward the event log, the endpoints will eventually check in with the log collector.
On the log collector, open the Event Viewer – Subscriptions. The number of “Source Computers” will increase over time.

Right-click and select “Runtime Status” to observe the individual endpoints.

Generating a control event
To test and verify the functionality of Windows Event Forwarding (WEF) and ensure that events are correctly forwarded to the ‘Forwarded Events’ logs, you can execute the following PowerShell command on one of the hosts within the domain:
Write-EventLog -LogName System -EventId 4624 -EntryType Information -Source "System" -Message "This is an event generated for WEF testing purposes"Note! This event uses the “System” event log instead of “Security”. Access to the security log is restricted and cannot be easily written. To test the above, an additional subscription is needed with the System event log selected.
Open the Event Viewer –> Forwarded Events to check for the generated test event.

Auditing and Group Policy requirements for NTLMv1 logging
To properly capture and log NTLMv1 events, advanced auditing must be enabled, and the correct Group Policy settings must be configured on the relevant Windows computers within the domain. Here are the requirements and steps:
Advanced auditing
Advanced auditing is a feature in Windows operating systems that allows detailed logging of specific events and actions on a computer. It provides more in-depth and accurate information than standard logging, enabling administrators and security professionals to gain detailed insights into system behavior and identify potential security issues.
The default configuration already activates the relevant settings. However, it is advisable to perform a preliminary check to ensure the desired auditing is present. Execute the following command-line:
auditpol.exe /get /category:Logon/Logoff
Note! Logon must have at least success enabled to generate the desired events.
NTLM Auditing in Group Policy
Ensure that the GPO with the configured audit policy settings is applied to the target computers. Link the GPO to the relevant organizational unit (OU).
In the policy, navigate to:
Computer Configuration -> Policies -> Windows Settings -> Security Settings -> Local Policies -> Security Options
- (All domain members, incl DCs):
Network Security: Restrict NTLM: Audit Incoming NTLM Traffic:
Enable auditing for domain accounts. - (All domain members, incl DCs):
Network Security: Restrict NTLM: Outgoing NTLM traffic to remote servers: Audit All. - (Domain Controllers only):
Network Security: Restrict NTLM: Audit NTLM authentication in this domain: Enable all.



Forcing NTLMv1 for testing purposes
Forcing NTLMv1 authentication within a managed domain requires specific steps and considerations to ensure it is done safely. This chapter focuses on the procedure and considerations for enabling NTLMv1 authentication for testing purposes within a Windows environment. The following steps are discussed to effectively manage this process.
Domain Controller
In a policy on the organizational unit for domain controllers, the group policy setting “Network security: LAN manager authentication level” should not be set to or should not have the maximum value of 5 “Send NTLMv2 response only/refuse LM”, any other setting is fine for testing.
Server class devices
Server class devices do not require changes as long as domain accounts are used for testing.
EndPoint devices
A Windows EndPoint device must have the value “Send LM & NTLM responses” in the group policy setting “Network security: LAN manager authentication level”.
A reboot is not strictly necessary.
Authentication test
From the Windows EndPoint device, open a CIFS/SMB share on an IP address or an HTTP(S) request on an IP address to an IIS web server configured for NTLM authentication. This server can be part of the created subscription, but it’s not a requirement as the DC handles the authentication.
The 4624 event will appear in the security event log of the DC where a connection is made. If properly configured, this event will be forwarded to the log collector within 30 seconds.
Troubleshooting
Although Windows Event Forwarding is a powerful tool for collecting and centrally managing Windows events, challenges and issues can sometimes arise during its implementation. This chapter is dedicated to identifying, diagnosing, and resolving problems that may occur with Windows Event Forwarding. I will cover various common issues along with steps and techniques to effectively address them. By becoming familiar with troubleshooting, you can ensure that the Windows Event Forwarding implementation runs smoothly and that important data is always available for analysis.
Event log locations
- Application and Services Logs – Microsoft – Windows
- EventLog-Forwarding Plugin (log)
- Windows Remote Management (log)
- Event Collector (log)
Firewall rules
- Windows Firewall ports Windows Remote Management (HTTP-In) Port 5985 configured for inbound communication.
- Windows Firewall ports Windows Remote Management (HTTP-In) – Compatibility Mode – Port 80 configured for inbound communication.
- Windows Firewall ports Windows Remote Management (HTTPs-In) configured for inbound communication.
Basic firewall connectivity
Test-NetConnection -ComputerName prod-mon.corp.michaelwaterman.nl -port 5985
Check WinRM connectivity
winrm id -remote:<source_computer_name> -auth:none
WinRM settings
WinRM client configuration
winrm get winrm/config/client/authWinRM server configuration
winrm get winrm/config/service/authWinRM service configuration
winrm get wmi/root/cimv2/Win32_Service?Name=WinRMReset WinRM to default
winrm invoke restore winrm/config @{}WinRM related security groups
- Local administration.
- Domain administrator
Display all registered machines to the subscription
wecutil gr <Subscription>
All about NTLM values
LM-manager (LM) authentication is the protocol used to authenticate Windows clients for network operations, including domain memberships, access to network resources, and user or computer authentication. The LM authentication level determines which challenge/response authentication protocol is negotiated between the client and server computers. Specifically, the LM authentication level determines which authentication protocols the client will attempt to negotiate or which the server will accept. The value set for LmCompatibilityLevel determines which challenge/response authentication protocol is used for network logons. This value affects the level of the authentication protocol used by clients, the level of session security negotiated, and the level of authentication accepted by servers.
| Value | Setting | Description |
|---|---|---|
| 0 | Send LM & NTLM responses. | EndPoints use LM and NTLM authentication and never use NTLMv2 session security. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 1 | Send LM & NTLM – use NTLMv2 session security if negotiated. | EndPoints use LM and NTLM authentication and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 2 | Send NTLM response only. | EndPoints use only NTLM authentication and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 3 | Send NTLMv2 response only.
(Windows 7+ default) |
EndPoints use only NTLMv2 authentication and use NTLMv2 session security if the server supports it. Domain controllers accept LM, NTLM, and NTLMv2 authentication. |
| 4 | Send NTLMv2 response only/refuse LM. | EndPoints use only NTLMv2 authentication and use NTLMv2 session security if the server supports it. Domain controllers refuse LM authentication and only accept NTLM and NTLMv2 authentication. |
| 5 | Send NTLMv2 response only/refuse LM & NTLM. | EndPoints use only NTLMv2 authentication and use NTLMv2 session security if the server supports it. Domain controllers refuse LM and NTLM authentication and only accept NTLMv2 authentication. |
Additional info
This chapter contains various references that are not included in the main part of the post and are intended to further support the NTLM traffic inventory process.
NTLM Registry key settings
- Key:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa - Value:
LmCompatibilityLevel - Type:
DWORD
PowerShell for auditing activation
# Audit NTLM Authentication in this domain: Enable all - Domain Controllers Only
Set-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\services\Netlogon\Parameters' -Name AuditNTLMInDomain -Value 7
# Audit incoming NTLM traffic: Enable auditing for all accounts
Set-ItemProperty 'HKLM:\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0' -Name AuditReceivingNTLMTraffic -Value 2
# Restrict NTLM: Outgoing NTLM traffic to remote servers: Audit All
Set-ItemProperty 'HKLM:\SYSTEM\CurrentControlSet\Control\Lsa\MSV1_0' -Name RestrictSendingNTLMTraffic -Value 1Final thoughts
Implementing Windows Event Forwarding (WEF) is a powerful way to enhance your organization’s security and monitoring capabilities. By centralizing event logs and focusing on NTLM v1 traffic, you can gain valuable insights into your network’s authentication processes and identify potential security risks.
While setting up WEF may require some initial effort and configuration, the benefits of having a comprehensive, real-time view of your network’s activities are well worth it. This guide has provided you with the necessary steps and considerations to get started, but remember that ongoing monitoring and adjustment are key to maintaining an effective security posture.
Windows Event Forwarding (WEF) allows you to collect event logs of windows based systems on a central server or SIEM. There are two operating modes for WEF;
Pull mode: In this mode, the WEF server goes and collects the logs on its own, which is not a preferred method as it will impose a load on the server.
Push mode: In this mode, clients send logs to WEF server over http TCP 5985 and https 5986 ports via WinRM service. The biggest advantage of this mode is that it will prevent performance problems as it does not create a load on the WEF server.
Collector Iniated(Pull mode): Starts the WEF server to collect logs. WEF server connects to clients and pulls logs on itself. This method is not recommended as it is not economical in terms of resource usage.
Source Computer Initiated(Push mode): Clients send their logs to the WinRM ports of the target WEF server (such as WinRM over HTTPS (TCP\5985) or WinRM over HTTP (TCP\5986)) via the WinRM service. This method is similar to transmitting log records with syslog. Here, the source is the clients, which is the source of the spent log, and these systems register to the WEF server with Kerberos Authetincation.
#Windows Remote Management (WInRM) enabled winrm qc #Configure Event Collection Services enable wecutil qc #You need to allow TCP 5985 and https 5986 ports over firewall. netsh advfirewall firewall add rule name="NETBIOS UDP Port 5985" dir=in action=allow protocol=UDP localport=5985 netsh advfirewall firewall add rule name="NETBIOS UDP Port 5986" dir=in action=allow protocol=UDP localport=5986
Computer Configuration >Polices > Administrative Templates > Windows Components > Event Forwarding” altında “SubscriptionManager Enabled
Computer Configuration -> Polices > Administrative Templates -> Windows Components -> Windows Remote Management (WinRM) -> WinRM Service -> Turn On Compatibility HTTP & HTTPS Listener Enabled
Computer Configuration>Windows Settings > Security Settings > System Services > Windows Remote management > Automatic
Let’s enter the following value in the Subscription Manager section. Of course, you will arrange it according to your own WEF server. (I redirected to DC)
Server=http://anatolia.guler.com:5985/wsman/SubscriptionManager/WEC,Refresh=60
After these processes, we open the Event Viewer on the server you have designated as the WEF server. From the Subscriptions section, we click on Create Subscription. From the Source Computer Initiated section, we configure the settings as seen. If there is a warning, it will probably be a warning that your disk and performance will decrease because you have chosen to take too many logs.
Note: If the log will be collected with the Collector Initiated method, the WEF server must be added to the “Event Log Readers” group with Restricted Groups as “Computer” account.

At the end of these processes, we will start to see our logs in Forwarded Events.
Faydalı olması dileğiyle — Hope it’s useful
This post is licensed under CC BY 4.0 by the author.
