Недавно я писал в Telegram и ВК о том, что Microsoft не тестирует Windows 10 с отключенным контролем учетных записей. Вдогонку я сделал опрос, где поинтересовался, включен ли UAC у читателей. В варианте для Telegram было три варианта ответа «Да», но только один вариант «Нет».
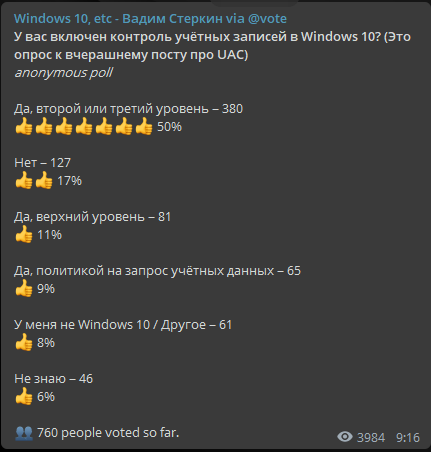
А следовало бы сделать два варианта, чтобы выяснить, какая доля от 17% выбравших пункт «Нет» пребывает в ложной уверенности 
Начиная с Windows 8, перемещение ползунка в нижнее положение в диалоге настройки UAC не отключает контроль учетных записей. Строго говоря, написанное на экране этого и не обещает. Причем в Windows 8 из информационного блока убрали фразу о том, что этот уровень имеет смысл использовать только в том случае, если приложения не поддерживают работу с UAC.
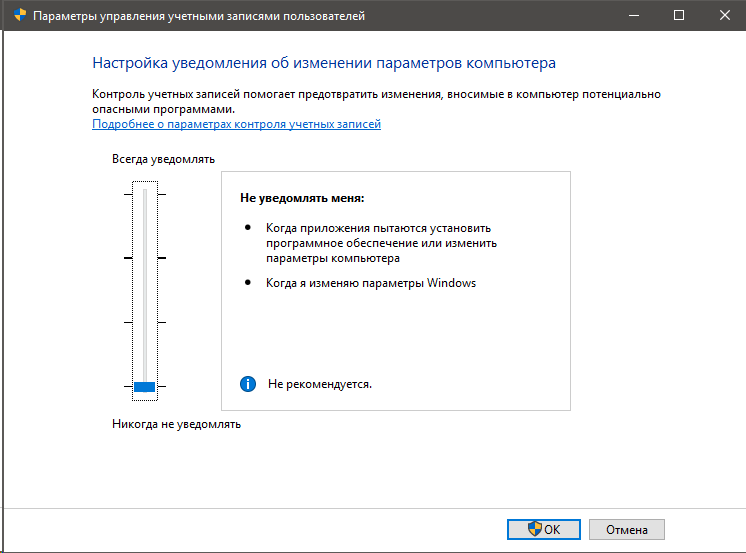
В этом положении отключаются только запросы UAC с вопросом Да/Нет.
В работе контроля учетных записей легко убедиться, сдвинув ползунок вниз и выполнив простые действия для проверки. Например, запустите cmd — в заголовке окна не будет написано «Администратор». Для полноты картины посмотрите в Process Explorer уровень целостности процесса — он будет средним.
Или скопируйте какой-нибудь файл в System32 в проводнике или стороннем файловом менеджере. Появится диалог, где будет кнопка со щитом, ведущая к успеху. Занятно, что запроса UAC вроде как нет, но все-таки от вас требуют подтвердить операцию правами администратора.
Это происходит потому, что по возможности используется токен обычного пользователя, а административный выдается только при запросе процессом полных прав. Когда вы копируете файлы, используются обычные права, но их не хватает для записи в системную папку. Поэтому Windows запрашивает полные права, а файловый менеджер делегирует решение вам.
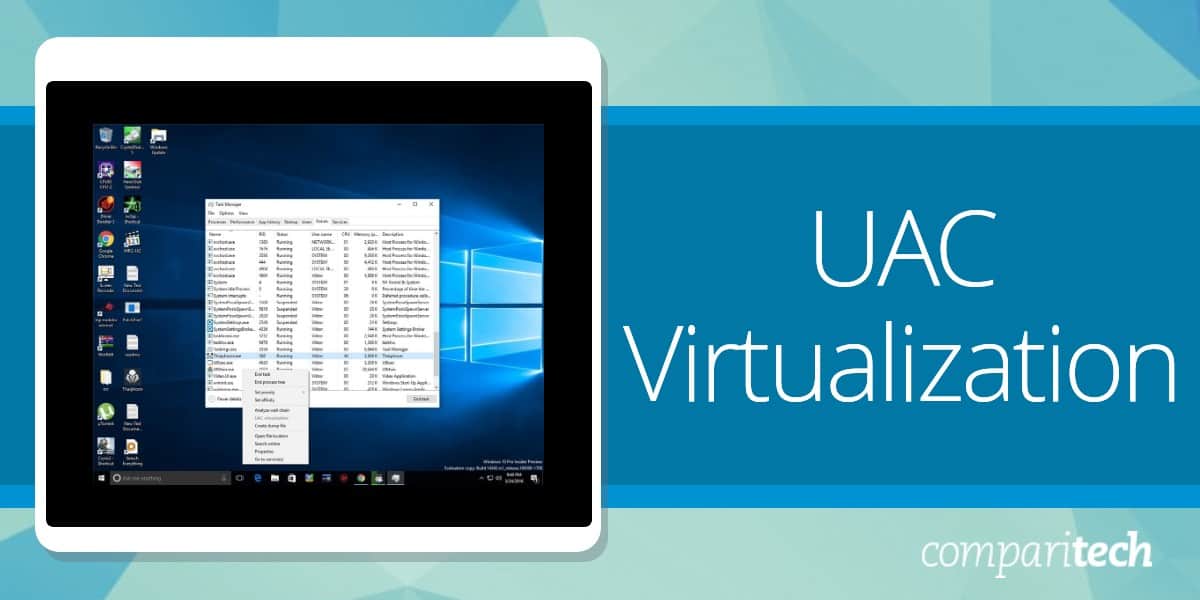
Виртуализация UAC
Виртуализация UAC тоже работает при отключении уведомлений. У меня самурайский менеджер буфера обмена Charu установлен в Program Files, там же он пытается создавать папки для пользователей и писать данные в них. Но виртуализация UAC перенаправляет все в профиль вне зависимости от положения ползунка.
Как процессы получают полные права
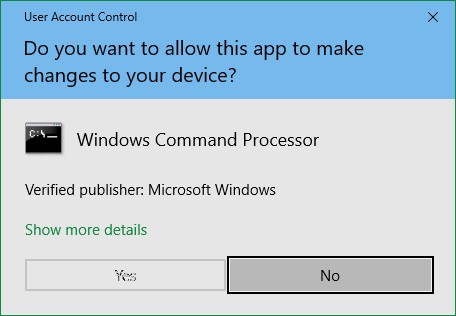
Попробуйте запустить командую строку от имени администратора с ползунком UAC в нижнем положении. В заголовке окна написано «Администратор», но при запуске запрос не появляется. В этом примере вы сами указываете желаемые права, но иногда за вас это делает приложение.
Установщики подавляющего большинства программ прописывают в манифесте уровень highestAvailable. В этом случае у администраторов установщик запускается с полными правами сразу, поэтому запись в системные расположения (Program Files) ведется без подтверждений.
В этом и заключается недостаток работы с отключенными уведомлениями UAC. Вы никак не контролируете запуск процессов с полными правами.
Резюме
Microsoft нашла баланс между комфортом пользователей и совместимостью приложений – старых и современных.
Именно магазинные приложения в Windows 8 подтолкнули к этому изменению!
С реально выключенным контролем учетных записей они не работали, и компания явно не хотела, чтобы ненависть к уведомлениям UAC блокировала встроенныe в ОС приложения и весь магазин. При этом в Microsoft предусмотрели вариант обновления со старой ОС, где единственный пользователь — встроенный администратор.
UAC отключается, конечно, но только политикой или в реестре. (При этом магазинные приложения в Windows 10 все равно запускаются, но виртуализация UAC отключена, конечно.) Однако дома никакого смысла в этом нет. Тем более, что Microsoft даже не рассматривает такой вариант работы.
Этому изменению в Windows уже 6 лет, и я подумывал написать о нем каждый раз, когда видел в форумах людей, пребывающих в ложной уверенности, что контроль учетных записей у них полностью отключен. Вот увидел в очередной раз и написал 
- сдвинул ползунок вниз, думая, что отключает UAC – вам комфортно работается?
- отключает UAC полностью – какую цель вы преследуете?
Небольшое объявление для тех, кто не зарегистрирован в Telegram / ВК / Twitter, но все-таки хочет читать, что я там пишу. Я добавил два источника контента — ленту RSS постов Telegram и Яндекс.Дзен.
What is UAC virtualization and when should it be deployed? We explain it in this topic.
Networking and Cyber Security Specialist
Updated: February 18, 2025
UAC stands for “User Account Control”. This is a field of software management that isolates the operating system’s core components from potentially damaging changes. This is the level of access that in Unix-like systems is called “root” and in Windows systems is known as Administrator privileges.
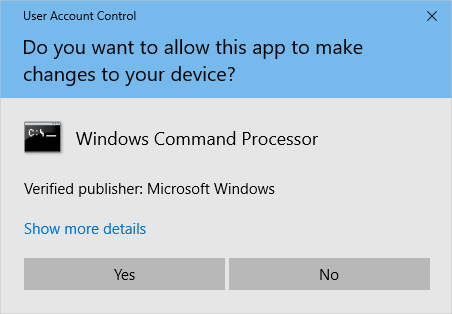
The most frequent encounter that users of Windows get with UAC occurs when they try to install a new piece of software. That popup message asking for authorization in order to permit the installation is the public face of UAC.
More about UAC
User Account Control has been integrated into Windows since Windows Vista in 2006 and it has been included in Windows Server since version 2008.
The UAC system lets user-installed software run in the user area of the drive and only software installed by the Administrator account gets access to system resources. Software that has been installed by the Administrator can be run by users without access to system resources or run by the Administrator to get that system access.
The purpose of UAC is to strengthen system security. It is assumed that the Administrator in a secure business environment is only accessible by an IT professional who will only install authorized, verified software. Users, on the other hand, can’t always be trusted to take precautions about what they download.
Users can easily be tricked into downloading malware that is embedded in an image or a PDF file. Without the Administrator privilege, software that gets access to the endpoint through a user account, will not be able to get into important services.
Areas of the disk that are blocked to user accounts include the %ProgramFiles%, %Windir%, %Windir%\system32 directories. The UAC service also blocks write access to the HKEY_LOCAL_MACHINE\Software\ registry path.
That permission popup is a key part of UAC. It triggers a setting in the operating system to either facilitate actions in the OS’s sensitive directories with permission or block that access if permission is refused.
System access should only be necessary during the installation and update of the software. Operating variables, temporary storage, and session data should all be stored in user-owned folders. System settings should only be written to a shared, editable folder, such as %programdata%.
The rigid organization of data and settings is beneficial to all users. If one user on a device is able to customize the software, those personal preferences do not impact the other users on that computer.
Can UAC be bypassed?
UAC was introduced to help prevent malware from gaining elevated access and executing malicious actions on the system. While UAC is an essential security mechanism, it is not foolproof, and in some cases, malware can bypass or exploit UAC to gain higher privileges and compromise a system.
There are several ways that malware can bypass Windows UAC, taking advantage of vulnerabilities in the system, user behavior, or flaws in the UAC mechanism itself. One common technique is the use of UAC bypass exploits, where malware takes advantage of bugs or design flaws in how UAC handles privilege escalation. For example, certain UAC prompts might be bypassed through specific registry manipulations or by exploiting misconfigurations in the Windows system.
Another method involves social engineering, where malware tricks users into granting administrative access, often by presenting a fake or misleading UAC prompt. For example, malware may disguise its process as a legitimate program, prompting the user to unknowingly grant elevated privileges. This can happen if the user is not cautious and does not verify the source of the application or prompt.
Additionally, advanced malware may employ fileless attacks, which execute malicious code directly in memory without relying on files that could be detected by antivirus software. These types of attacks are harder to detect and can bypass traditional UAC checks.
While Windows UAC is a valuable security feature, it is not a comprehensive solution to all malware threats. Users must remain vigilant about the software they install, maintain regular system updates, and use extensive security software to minimize the risk of UAC bypass and other security breaches.
Virtualization
There are a number of types of virtualization. The general purpose of this strategy is to use the software in order to create an environment that mimics a real resource, such as a separate server or a PC’s hardware.
One of the most widely implemented types of virtualization is a “virtual machine,” or VM. This is a separate operating system that floats on top of the real OS. It gives the services that a piece of software needs from the operating system without letting that software get real, direct access to the actual OS.
The VM mediates between the software and the operating system. In some instances, this configuration can enable software written for one operating system to run on a computer that doesn’t actually have that operating system installed. For example, it is possible to run software that is written for Linux on a computer that has the Windows operating system. If a virtual environment is available to interpret the Linux- compatible demands of the software into requests the Windows can understand – it is like an interpreter.
UAC virtualization
In the case of a UAC virtualization, the VM operates Windows and runs on top of Windows. The purpose of the double operating system isn’t to provide compatibility in OS but to cater to validated legacy software that genuinely needs access to those system areas when run by users.
Rather than mediating between two different operating systems, the UAC virtualization provides the services that the software needs to run in a user account without breaking the strict system isolation of UAC. Access to the folders that the software needs is blocked and that fact would cause the program to hang or fall over.
The implementation of UAC virtualization was a necessary step in order to bridge the introduction of User Access Control. Without this stop-gap measure, much of the software built to run on Windows would cease to function. Although software houses would, in time come to write new versions of their products, the complete rewrite that UAC required would have taken time. Such major changes are usually reserved for new editions and are not accounted for as updates.
Software houses that specialized in products for Windows could not afford to write off the investment already made in their products. When new editions are produced, the vendors calculate a service life for them and wait until all costs have been recovered before writing new versions.
The UAC virtualization maps between the system folder demands of legacy software and the user-owned folders that Windows now expects software to use when run from user accounts.
Thanks to the UAC virtualization, software that writes to C:\Program Files\, is really writing to %LOCALAPPDATA%\VirtualStore\. Thus, a mapping interface between folders in the virtualization keeps old software working while protecting reserved system directories.
The Application Manifest
Not all software is going to need access to protected system areas. Some programs download as executable files and run from wherever they are resident on the computer. The main issue of whether or not a program needs to write files to reserved directories comes down to a matter of the organization of folder access needs.
The installer signals to the operating system what folder access the program expects both for installation and whenever it is run through entries in the Application Manifest. This is an XML document that accompanies the programs in an installer package.
A permission level requirement value within the file is the key to whether Windows will invoke UAC virtualization for this program whenever it is run. Possible values for requestedExecutionLevel are:
- asInvoker Run with the same access token as the parent process.
- highestAvailable Acquire the highest privileges the current user can obtain.
- requireAdministrator This program can only run as Administrator.
Windows will always use UAC virtualization for software that is flagged with the requireAdministrator access need. This type of software will always provoke the appearance of the UAC permission popup whenever it is run. This status is the default. So, if there is no application manifest, or the required execution permission statement is missing, the software will automatically have the requireAdministrator status and will always be virtualized.
When UAC virtualization is invoked
UAC virtualization is a mechanism within Windows, it can’t be applied at will. There is no UAC hypervisor package in circulation. It isn’t a utility in a developer framework and there isn’t an API for it. In short, you can’t command the use of UAC virtualization.
The UAC virtualization process doesn’t apply to all software. Here are some circumstances to keep in mind over whether UAC virtualization will be used for an application:
- UAC Virtualization is only invoked for software when it is run from a user account. Applications running as Administrators don’t need it.
- UAC Virtualization has to be enabled and active on the host.
- Programs running in a 64-bit environment don’t need UAC virtualization. It only applies to 32-bit software.
- The user account needs to have write access to the files in the original file path.
Managing User Account Control
The User Account Control behavior can be modified on each computer that runs Windows. This option is available in the Settings menu and you can get to it by clicking on the Settings cog icon in the Start menu and then typing User Account Control into the Settings search bar.
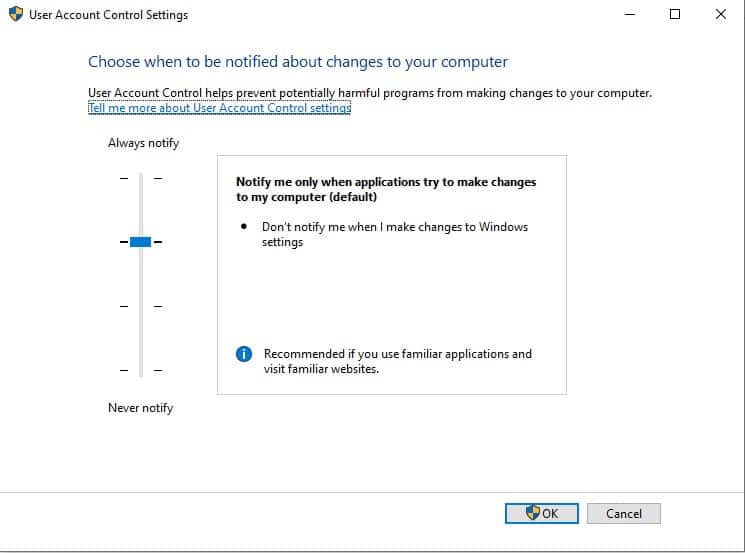
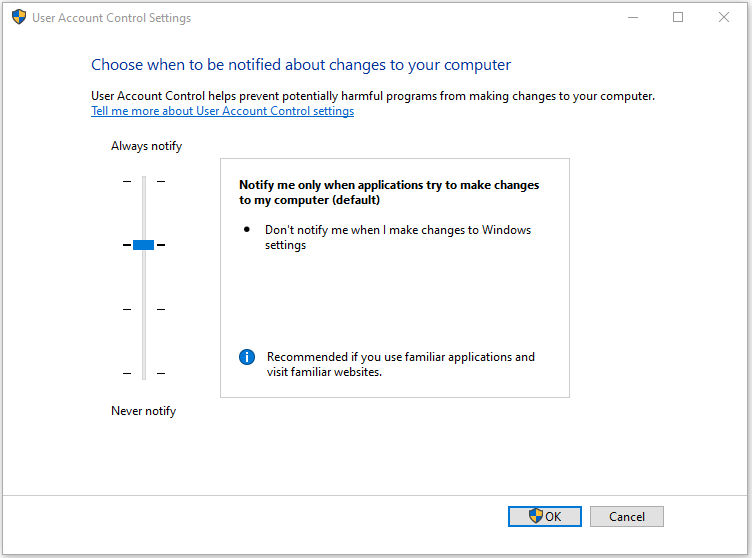
The User Account Control settings screen is presented as a slider. This gives the user the option of switching between one of four settings for UAC. These options are:
- Always notify
- Notify me only when programs try to make changes to my computer
- Notify me only when programs try to make changes to my computer (do not dim my desktop)
- Never notify
Below, you will find a little more detail about each of these options.
Always notify
This is the most rigid setting. It invokes the notification popup when a program is about to be installed or updated and when you, or any programs, try to change Windows settings. It will freeze all tasks on the computer until you respond.
This option is recommended for computers where new software is frequently installed and for people who visit unfamiliar websites.
Notify me only when programs try to make changes to my computer
This is the default value for UAC. It will notify the computer’s user when programs try to install software or make changes to your computer. It won’t put up the permission popup when you make changes to your computer’s settings yourself. It will freeze all tasks on the computer until you respond.
This option is recommended for those who frequently install new software and visit unfamiliar websites, but don’t want to be notified over their own actions that alter Windows settings.
Notify me only when programs try to make changes to my computer (do not dim my desktop)
This option provokes the permissions popup when programs try to install software or make changes to the computer but it won’t notify those users who make changes to Windows settings manually. Unlike the previous two options, this setting will not freeze other tasks or wait for a response.
This option is only recommended if, for some reason, the notification process works slowly on the computer to the point where it becomes a serious inconvenience to the user.
Never notify
This option disables User Access Control. You will not get the permissions popup under any circumstances.
This option creates a security risk.
Registry Virtualization
Registry virtualization is the application of UAC virtualization to the system registry. The purpose of this feature is to block access to global registry entries while enabling software that requires such access to continue to function. As UAC interprets folder access and diverts write actions to user-controlled directories, Registry virtualization switches attempts to write to global variables to safer user account registry keys.
As with file-based UAC virtualization, the software proceeds with all of its pre-written procedures, creating and updating registry key values without harming those global registry areas.
Registry virtualization is only implemented in order to enable legacy systems to continue operating. The need for this service is probably, by now, almost completely defunct. Any software that was written after 2006 will not need the registry virtualization service because it should have been written along with Microsoft developer guidelines. These guidelines explain the difference between global registry entry use and the registry keys that are available to user accounts.
The future of UAC virtualization
UAC virtualization was created to ensure backward compatibility when Microsoft launched its new architecture. It is a method for preventing legacy software from failing because they are no longer permitted to write to the files whose paths and names are hardcoded.
This shows that UAC virtualization has no future – it is all about the past. The UAC virtualization system has become progressively more redundant as time passes. As UAC has been part of Windows since 2006, it has been an environmental certainty for 25 years. The chances of software written more than 25 years ago still being active without any new versions or updates are slim. For one thing, old software is very prone to attack by hackers. Vulnerability scanners particularly look for old software when probing computers and networks for a way in.
UAC virtualization in Windows 10
If you are running Windows 10 you might decide to search for your UAC virtualization setting and see whether the function is turned on.
In order to do this:
- Press the Windows button plus “R” to open a Run box.
- Type secpol.msc and press “OK” to open the Local Security Policy app.
- In the Local Security Policy window, expand Local Policies and click on Security Options in the left panel.
- Scroll down the list of policies in the main panel until you get to User Account Control: Virtualize file and registry write failures to per-user locations.
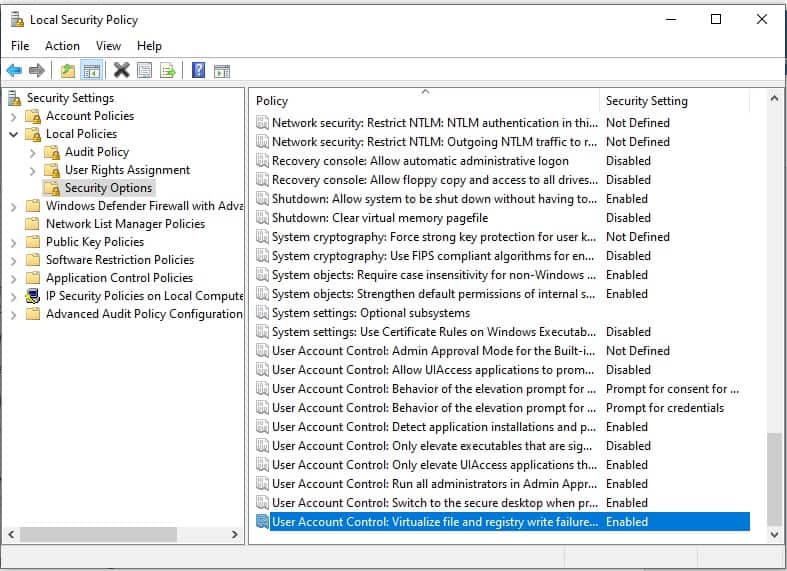
The status of this setting should be Enabled. If it isn’t:
- Double-click on the User Account Control line. A popup will appear.
- Click on the Enabled radio button.
- Click OK to close the popup.
Other system protection methods
A typical Windows user shouldn’t need to worry about UAC virtualization and a designer of software that is intended for use on Windows also need not be concerned with UAC virtualization because current Windows programming practices make this service unnecessary.
There is a comprehensive Windows Security system that protects devices from tampering and there are a few settings that you can look at within Windows in order to improve system protection.
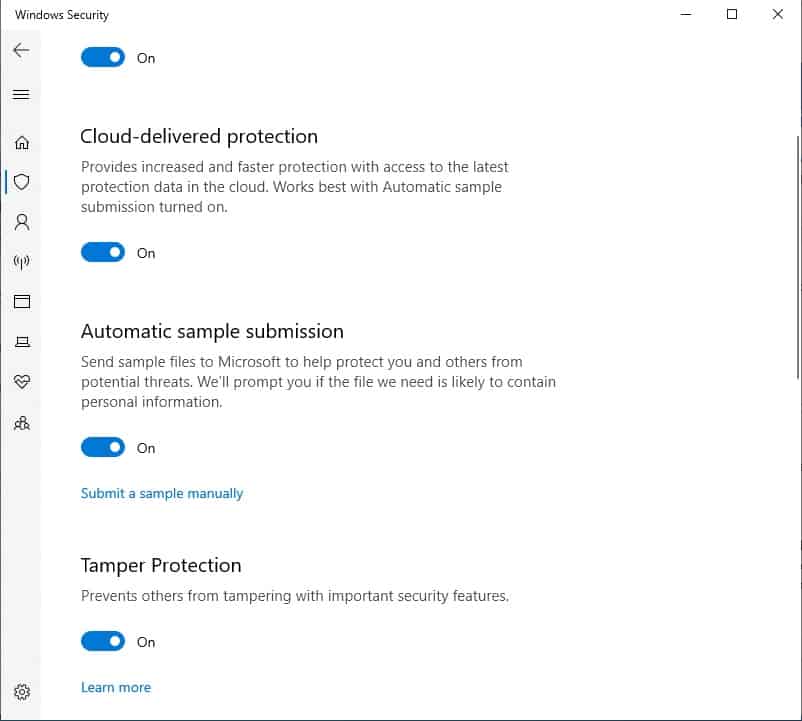
The first one that you could look at is Tamper Protection, which blocks malware from interfering with and altering your device’s antivirus settings. To check that this is turned on:
- Type Windows Security in the Start menu search field.
- Select the Windows Security app from the results.
- Click on Virus & threat protection.
- Look to the bottom of the main panel on this screen and click on Manage settings.
- Tamper Protection is the fourth option on this screen. Make sure it is turned on.
You should also ensure that Real-time protection, Cloud-delivered protection, and Automatic sample submission are turned on.
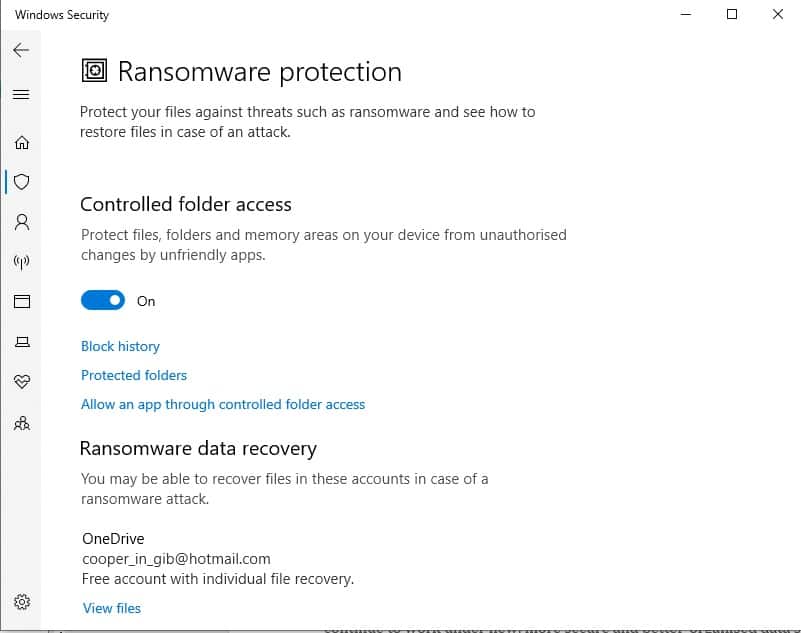
The other major substitute for UAC virtualization protection is the Controlled folder access system. This prevents malware from changing the extensions on files to hide them or altering system folder names. This can also be accessed from the Virus & threat protection settings screen where you turned on Tamper protection.
- In the Virus & threat protection settings screen. Scroll down to Manage controlled folder access and click on it.
- In the next screen, which is Ransomware protection, move the slider for Controlled folder access to On.
- You will be taken to the User Account Control permission popup. Click on Yes to allow the change.
Conclusion
UAC virtualization was a stop-gap measure that enabled the large library of software available for Windows to keep operating. Without this solution, a large amount of the applications available for Windows would have stopped working when Windows Vista was introduced.
With the passage of time, UAC virtualization has become increasingly unnecessary. However, as you have seen, it is still in Windows 10 and you probably will see that it is enabled on your computer.
The virtualization solution for UAC was a clever one and its methods would prove useful to any system protection scenario. In fact, many security systems operate on virtualization, classifying them as “virtual appliances.” The isolation of the operating system and applications works both ways. It can also prevent hackers from getting into the software and tampering with them by blocking off the access route through the operating system.
UAC virtualization FAQs
Should I disable UAC virtualization?
UAC virtualization is a fundamental element of Micorosft’s security strategy for Windows. Turning UAC off loses you the benefit of native security procedures.
How do you make an executable not subject to UAC virtualization?
There are two ways that an executable can be exempted from UAC virtualization. The first is to design the software as a portable package that doesn’t need to be installed but will run as a file in the location where it was downloaded. The other way to avoid UAC virtualization kicking in when the program runs. The other way is to include an Application Manifest with its installer. This should contain an entry for requestedExecutionLevel with a value set at asInvoker or highestAvailable.
Здравствуйте уважаемые! Хотелось бы рассказать немного про один из механизмов защиты ОС.
Наверняка многие не по наслышке знаю что это такое, но надеюсь так же многие подчеркнут для себя что то новое из этого топика, и так приступим!
UAC (User Account Control) — это средство контроля пользовательских учетных записей, впервые появившийся в Windows Vista.
Главная задача UAC была — заставить всех работать как обычный стандартный системный пользователь, т.к. работа с правами администратора очень не безопасна. Все мы прекрасно знаем, что многие приложения с которыми мы работаем могут содержать «уязвимости» и их же часто используют злоумышленники. Соответственно работая это приложение с правами администратора (хотя за частую приложениям не требуются права такого уровня), может писать в системные папки абсолютно прозрачно для пользователя, чего нам собственно и не нужно. Для воизбежания подобных ситуаций собственно и был призван на помощь UAC.
Он не только защищает вас от злонамеренного кода, а так же в какой то мере оказывает совместимость со «старыми» приложениями. Он позволяет писать «старым» приложения в системные папки, а если быть точнее эти приложения просто так думают что пишут в системные папки, но на самом деле пишут в виртуализированные папки, в следствии чего приложения работают вполне корректно.
Как работает UAC ?
Собственно когда вы заходите в систему, создаются 2а маркера доступа: административный и обычный.
Административный лежит в загашнике, а вы работаете под обычным аккаунтом. Далее если вам потребуется повышение привилегий, возникает защищенный рабочий стол и внутри этой сессии вы делаете выбор «Да, я согласен» или «Отмена». Это сделано для предотвращения спуфинг атак. Если в систему заходит обычный пользователь, то для него административный маркер не создается, а только обычный. Затем если ему нужно повысить свои привилегии, снова появляется защищенный рабочий стол в котором запрашивается пароль административной учетной записи. После чего для приложения формируется административный маркер доступа. По завершению приложения, административный маркер доступа удаляется.
Виртуализация UAC
Хочу напомнить, что отключая user account control вы подвергаете всю систему опасности и превращаете вашу ОС в windows XP, а не просто отключаете надоедливые окошки.
При этом отключая UAC вы выключаете windows resource protection, который собирает все необходимые для «жизни» файлы в хранилище, что бы после критического сбоя восстановить поврежденные файлы.
Виртуализация осуществятся в режиме ядра.
* Файловая система: драйвером luafv.sys.
* Реестр: встроенными средствами.
Перенаправляемые каталоги системы:
\Program Files, \Windows, \Windows\System32.
Исключения: Системные *.exe и *.dll.
Перенаправляемые разделы реестра:
HKLM\Software
Исключения: Некоторые ключе подраздела Microsoft.
Приложение работающее с обычными правами, перенаправляет в:
* Запись:
\Users\\AppData\Local\Virtual Store
HKCU\Software\Classes\VirtualStore
Что совершенно прозрачно происходит для самого приложения, т.е. приложение продолжает думать что оно пишет к примеру в \Program Files.
* Чтение:
Сначала используется зона пользователя, затем глобальное расположение.
Повышение привилегий для определенного приложения:
* В свойствах ярлыка поставить галочку «Запускать от имени администратора».
* Эвристическим инсталлятором.
* Явным запросом пользователя.
* В манифесте.
Ну и в довершение неполный список действий, вызывающих сообщение User Account Control:
* Изменения в каталогах %SystemRoot% и %ProgramFiles% — в частности, инсталляция/деинсталляция ПО, драйверов и компонентов ActiveX; изменение меню «Пуск» для всех пользователей.
* Установка обновлений Windows, конфигурирование Windows Update.
* Перенастройка брандмауэра Windows.
* Перенастройка UAC.
* Добавление/удаление учётных записей.
* Перенастройка родительских запретов.
* Настройка планировщика задач.
* Восстановление системных файлов Windows из резервной копии.
* Любые действия в каталогах других пользователей.
* Изменение текущего времени (впрочем, изменение часового пояса UAC не вызывает).
Для написания данного топика использовался доклад Бешкова Андрея(Сотрудник microsoft), Википидия, собственные наблюдения.
-
Home
-
Knowledge Base
- What Is UAC Virtualization and How to Enable It on Windows?
By Daisy | Follow |
Last Updated
UAC virtualization protects your PC from malware. It also reduces unauthorized changes to the operating system. All in all, it adds an extra layer of security to your device. This post provides more details about UAC virtualization for you.
What Is UAC Virtualization?
What is UAC virtualization? In 2007, Microsoft Windows Vista introduced a new security feature called User Account Control (UAC). UAC virtualization is an area of software management that isolates core components of an operating system from potentially disruptive changes. It refers to the level of access called “root” on Unix-like systems and administrator privileges on Windows systems.
Windows UAC rules are designed to protect installed program files and registry settings from modification or corruption by users or programs that should not be accessed; separate each user’s files and settings from other users.
By default, only users with administrator privileges can access the main machine settings. Microsoft enforces these rules by carefully restricting the default permissions for folders under the Program Files folder tree, Program Data folder tree, Windows folder tree, and Users folder tree. Additionally, permissions on registry keys are carefully restricted so standard users are not allowed to modify any settings that could affect other users.
Limitations of UAC Virtualization
To ensure that UAC virtualization works properly, there are some limitations of UAC virtualization:
- For 32-bit applications only. AMD64 compatible applications are all created after these fundamental design decisions and, by their very nature, cannot be written to address system files in the “old way” that UAC virtualization was created to solve. (IA64 applications have their own special set of problems.)
- The user must have write access to the file in the original file path. Attempting to write to any file with read-only permissions will crash the entire card library (i.e. cause the app to crash with an error code).
- UAC virtualization cannot be applied to applications run as administrators or elevated in any way – it must run in the context of a standard user.
- UAC virtualization is disabled by default – it must be explicitly enabled.
You can disable UAC virtualization in Task manager, but it is not recommended. If you disable UAC virtualization, some applications may not work for standard users. When the application tries to write to the directory, but the user does not have permission to write to the directory, it will change the path.
How to Enable UAC Virtualization in Windows 10
First, you need to check if you have enabled UAC virtualization on Windows 10. If not, you can choose enable it.
- Press the Windows + R keys together to open the Run dialog box and type secpol.msc. Then, it will open the Local Security Policy window.
- Expand Local Policies on the left-hand pane and click Security Options.
- Navigate to User Account Control: Virtualize file and registry write failures to per-user locations on the center pane.
If this option is enabled, UAC virtualization is set up on your device. If it isn’t, you can follow these 3 steps to enable UAC virtualization:
- Double-click User Account Control: Virtualize file and registry write failures to per-user locations. That opens a pop-up window
- Select the Enabled radio button
- Click OK to close the popup window. That enables UAC virtualization on your device
After setting up UAC virtualization, you can also manage its behavior and customize it to meet your preferences.
1. Always notify
This is the strictest setting. You must provide explicit permission when you or the software attempts to install, update, or change Windows Settings. All other tasks on the system will freeze until you respond with a notification popup. This setup is ideal for devices that frequently install software for testing.
2. Notify me only when programs try to make changes to my computer
This is the second most restrictive option. It is also the default UAC setting. Here, the computer will notify you when programs try to install or change Windows settings. Like the previous option, it freezes all tasks until you respond. However, this option does not generate a notification when you manually change any settings.
3. Notify me only when programs try to make changes to my computer (don’t darken my desktop)
As the name suggests, this option is non-intrusive and doesn’t freeze other tasks. It will also notify you when you manually make changes to your Windows system. Needless to say, this is a lower security option compared to the first two. Ideally, select this option only if you are the only user and the notification process is slow enough to affect your productivity.
4. Never notify
This option disables UAC virtualization, which poses a serious security risk to your device. We recommend against using this option, even if it seems convenient. All of these options are related to installing and changing software for Windows systems, especially restricted directories.
About The Author
Position: Columnist
Having been an editor at MiniTool since graduating college as an English major, Daisy specializes in writing about data backups, disk cloning, and file syncing as well as general computer knowledge and issues. In her free time, Daisy enjoys running and going with friends to the amusement park.
UAC is an innovative solution that helps users utilize legacy software and the latest Windows operating system. At the heart of UAC virtualization are security and compatibility. Unfortunately, many organizations don’t understand how UAC virtualization protects operating systems and user accounts.
This post will give your business an understanding of what UAC virtualization is, why it is crucial to protect system files, and some of the limitations inherent in UAC virtualization.
However, before we can explain and explore UAC virtualization, we must understand User Account Control (UAC) and how it interacts with the Windows operating system.
Gaining an Understanding of User Account Control (UAC)
If you have ever used Windows systems, you are likely familiar with a UAC prompt. A UAC prompt is a popup message asking for authorization when installing software
Essentially, this UAC prompt is a request from the operating system to the user to enable software applications to have specific device permissions
User Account Control was first introduced in Windows Vista. The idea was to minimize system-wide changes and only allow users with administrator privileges to give or take away these permissions.
Typically, the software won’t need to access system paths. As a result, Windows restricts this access with User Account Control. This made Windows Vista and the operating systems that followed it more secure than Windows XP.
With User Account Control, software that attempts to write to any system path will automatically fail. If the software requires this access to properly execute program files, a UAC prompt will appear, asking users if the software should be allowed the access it wants.
Generally, this will happen when a new software update is required.
UAC instantly made Windows systems more secure. Before UAC, the software could write anywhere on the device without checks or balances.
For example, a malicious program could manipulate system files, corrupt installed program files, stop software installed on the device, and even download or remove programs. Such access posed a significant security risk to users.
Windows UAC rules protect installed program files, user accounts, and system registry settings from being damaged or modified by unauthorized users or programs.
While the User Account Control improvements released after Windows Vista gave devices more security options and greater control over administrator privileges, there were some issues with legacy software.
UAC virtualization was developed to address the issues new UAC security options caused with legacy programs and systems.
UAC Virtualization Defined
With the introduction of UAC, the write access for many legacy programs changed, and these programs could no longer function properly. This caused a significant problem for organizations reliant on these legacy programs.
UAC virtualization provides the user access control legacy programs require to function without breaking the strict system isolation created by UAC.
UAC virtualization essentially fools legacy programs into thinking they have user path file and registry write access when they don’t. UAC virtualization can also be applied to the system registry through registry virtualization.
Windows registry virtualization blocks access to global registry keys and files while allowing programs that require access to the registry to continue functioning.
Windows 10 and 11 include file and registry virtualization technologies for programs that are not UAC-compliant and require an administrator’s access token to function as expected.
How to Enable UAC Virtualization
UAC virtualization features are disabled by default, so if you want to disable UAC virtualization, you don’t have to take any action.
To enable UAC virtualization, you need to visit the Control Panel. Once the Control Panel menu is open, follow this path: Configuration/Policies/Windows Settings/Security Settings, Local Policies, and Security Options.
Here you will find an option that reads, “User Account Control: Virtualize file and registry write failures to per-user locations.” Next, click the box that reads “Enabled,” and now you have enabled UAC virtualization.
If you want to disable UAC virtualization at any time, just follow these steps and click on the option to disable UAC virtualization.
Disabling UAC virtualization is not a great idea because it makes your system vulnerable to malicious programs and attacks. In addition to the security issues, some programs will not function correctly without UAC virtualization.
The Problems With UAC Virtualization
Although UAC virtualization makes systems more secure and enables legacy programs to function as expected, there are issues with UAC virtualization that should be addressed.
The primary issues with UAC virtualization include the following:
- Permissions – For UAC virtualization to work correctly, users must have access to the files within the original file path. Any attempt to write to read-only files could lead to errors and software crashes.
- 32-bit only – UAC virtualization will only work on 32-bit apps.
- Administrator – For UAC virtualization to function correctly, users cannot run the app with administrator privileges. UAC virtualization only works on standard user accounts.
However, the biggest issue with UAC virtualization is that it has to be manually enabled in the local security policy window with the “Virtualize file and registry write failures to per-user locations” option.
Unless you are savvy enough to understand these Windows settings, you likely won’t know to turn this feature on, which is a big issue.
Common Questions
We understand that the topic of UAC virtualization is very technical and can be confusing. As a result, we have collected some of the most common questions regarding this topic to help answer lingering questions you may have or clear up any information that might be confusing.
What happens when I enable UAC virtualization on my computer?
When you enable UAC virtualization on your computer you allow legacy applications to function in the modern UAC environment. Essentially, UAC virtualization automatically reroutes file access requests from the program path target to the new user data path.
Can UAC virtualization be disabled on my computer?
Yes, if you want to disable UAC virtualization, it is possible to do so. However, tech experts strongly recommend that you don’t disable this because doing so may cause certain applications to perform erratically or stop working entirely.
Windows users can quickly disable or enable UAC virtualization from the Task Manager. If you’re unsure if you need UAC virtualization, it is best to leave this setting untouched to ensure that you are not affecting the performance of your applications.
Are there any times when it would be recommended to disable user account control virtualization?
In specific situations, it may be necessary to disable user account control virtualization on Windows Server. According to the documentation provided by Microsoft, users should only disable UAC virtualization when both of the following conditions are met:
- Administrators have the sole ability to sign into the Windows Server using Remote Desktop Services or interactively at the console
- Administrators only sign into the Windows Server to perform system administrative tasks on the server
If both of these conditions are not met, UAC virtualization should not be disabled. If you’re unsure if you are meeting these conditions, it is best to leave UAC virtualization alone since it is likely not affecting your tasks in any perceivable manner.
Will UAC interfere with the Process Monitor tool?
Microsoft’s Process Monitor is used to help trace newly created processes. Users must have administrator privileges to use Process Monitor. As a result, when Process Monitor is started, you might get a UAC prompt that asks if you want to start the application.
However, UAC should not interfere with the functionality or performance of the Process Monitor.
Will UAC Virtualization affect the performance of my computer system?
The effect any tool or solution will have on computer system performance is something that should be accounted for. However, UAC virtualization will not affect the performance of your computer system because it doesn’t require additional computing resources to run.
If you are concerned about performance, you don’t have to worry about UAC virtualization. This feature will not hamper the performance of the system in any way or consume valuable computing resources.
Can UAC virtualization cause compatibility problems with some applications?
It is possible that UAC virtualization will cause compatibility issues with certain applications or programs. If you experience compatibility issues, you should try disabling UAC virtualization for that specific application or program.
If that does not resolve your compatibility issues, it is likely that UAC virtualization is not the culprit behind the compatibility problems you are experiencing.
Is it possible to run programs without getting a UAC prompt?
You need administrator privileges to run programs without getting a UAC prompt. You’ll need to run apps as an administrator while logged into an administrator account to bypass the prompt.
The way to bypass this prompt is to create a scheduled task with higher privileges for each program you want to run. Then you must manually invoke the scheduled task item by utilizing schtasks.exe.
For most users, this is a lot of unnecessary steps. However, if you are an administrator that wants to avoid the UAC prompt, you can follow these steps to bypass it.
Can UAC virtualization be disabled in Windows XP?
No. UAC virtualization cannot be disabled in Windows XP because this feature was not introduced at the time XP was launched. UAC virtualization would not be introduced until the release of Windows Vista.
If you are seeing a pop-up Window that is preventing you from installing programs or making changes to the system settings in Windows XP, it is not a UAC issue, but rather a case of using the wrong privileges.
In Windows XP you need an administrator account to install programs or make changes to the system settings.
What is the Windows Registry?
The Windows Registry is a hierarchical database. This database is utilized to store the low-level settings for the Microsoft Windows operating system and the applications or programs that opt to use the registry.
Can the Windows Registry be virtualized?
Yes. Registry virtualization is the application of UAC virtualization to the system registry. While it is possible to do this, this approach won’t be beneficial for most businesses.
How can UAC settings be changed on my computer?
If you are interested in editing the settings for UAC virtualization on your computer, you can try the following steps. First, press the Windows button plus R at the same time. This will open the run window on your computer.
Next, type in “Control Panel” and click OK. This will open a window or list. Choose the option that says “User Account.” Click the option that says “User Accounts (Classic View).” Then you will select the option that says “Change user account control settings.”
At this point, you might receive a UAC prompt. If you do, click “Yes” to continue. Now you will be given an option to set the UAC to “Never Notify” or “Always Notify.” If you want to turn the UAC off, select the never option. You can select the always option to turn the UAC on.
Finally, you must restart the computer system in order to finalize any changes that were made to the UAC settings.
Final Thoughts
If UAC virtualization seems overwhelming to you, don’t worry. UAC virtualization is slowly being phased out as Windows moves further away from Vista, and enterprise software is built to modern standards. UAC virtualization was never meant to be a long-term solution, just a temporary solution to ensure legacy programs would still function properly.If you want to learn more about UAC virtualization and how it impacts your organization, reach out to a skilled technical partner like Koombea.
