-
Notifications
You must be signed in to change notification settings -
Fork
1 -
Star
0
Appendix L: Events to Monitor >Applies to: Windows Server 2022, Windows Server 2019, Windows Server The following table lists events that you should monitor in your environment, according to the recommendations provided in [Monitoring Active Directory for Signs of Compromise](../../ad-ds/plan/security-best-practices/Monitoring-Active-Directory-f…
0
stars
1
fork
Branches
Tags
Activity
Notifications
You must be signed in to change notification settings
Repository files navigation
Windows-Event-ID-List
Appendix L: Events to Monitor >Applies to: Windows Server 2022, Windows Server 2019, Windows Server The following table lists events that you should monitor in your environment, according to the recommendations provided in Monitoring Active Directory for Signs of Compromise. In the following table, the «Current Windows Event ID» column lists the event ID as it is implemented in versions of Windows and Windows Server that are currently in mainstream support. The «Legacy Windows Event ID» column lists the corresponding event ID in legacy versions of Windows such as client computers running Windows XP or earlier and servers running Windows Server 2003 or earlier. The «Potential Criticality» column identifies whether the event should be considered of low, medium, or high criticality in detecting attacks, and the «Event Summary» column provides a brief description of the event. A potential criticality of High means that one occurrence of the event should be investigated. Potential criticality of Medium or Low means that these events should only be investigated if they occur unexpectedly or in numbers that significantly exceed the expected baseline in a measured period of time. All organizations should test these recommendations in their environments before creating alerts that require mandatory investigative responses. Every environment is different, and some of the events ranked with a potential criticality of High may occur due to other harmless events.
About
Appendix L: Events to Monitor >Applies to: Windows Server 2022, Windows Server 2019, Windows Server The following table lists events that you should monitor in your environment, according to the recommendations provided in [Monitoring Active Directory for Signs of Compromise](../../ad-ds/plan/security-best-practices/Monitoring-Active-Directory-f…
Resources
Readme
Activity
Stars
0
stars
Watchers
1
watching
Forks
1
fork
Windows event ID 4608 — Windows is starting up
Windows event ID 4609 — Windows is shutting down
Windows event ID 4610 — An authentication package has been loaded by the Local Security Authority
Windows event ID 4611 — A trusted logon process has been registered with the Local Security Authority
Windows event ID 4612 — Internal resources allocated for the queuing of audit messages have been exhausted, leading to the loss of some audits
Windows event ID 4614 — A notification package has been loaded by the Security Account Manager
Windows event ID 4615 — Invalid use of LPC port
Windows event ID 4616 — The system time was changed
Windows event ID 4618 — A monitored security event pattern has occurred
Windows event ID 4621 — Administrator recovered system from CrashOnAuditFail. Users who are not administrators will now be allowed to log on. Some auditable activity might not have been recorded
Windows event ID 4622 — A security package has been loaded by the Local Security Authority
Windows event ID 4624 — An account was successfully logged on
Windows event ID 4625 — An account failed to log on
Windows event ID 4634 — An account was logged off
Windows event ID 4646 — IKE DoS-prevention mode started
Windows event ID 4647 — User initiated logoff
Windows event ID 4648 — A logon was attempted using explicit credentials
Windows event ID 4649 — A replay attack was detected
Windows event ID 4650 — An IPsec Main Mode security association was established
Windows event ID 4651 — An IPsec Main Mode security association was established
Windows event ID 4652 — An IPsec Main Mode negotiation failed
Windows event ID 4653 — An IPsec Main Mode negotiation failed
Windows event ID 4654 — An IPsec Quick Mode negotiation failed
Windows event ID 4655 — An IPsec Main Mode security association ended
Windows event ID 4656 — A handle to an object was requested
Windows event ID 4657 — A registry value was modified
Windows event ID 4658 — The handle to an object was closed
Windows event ID 4659 — A handle to an object was requested with intent to delete
Windows event ID 4660 — An object was deleted
Windows event ID 4661 — A handle to an object was requested
Windows event ID 4662 — An operation was performed on an object
Windows event ID 4663 — An attempt was made to access an object
Windows event ID 4664 — An attempt was made to create a hard link
Windows event ID 4665 — An attempt was made to create an application client context
Windows event ID 4666 — An application attempted an operation:
Windows event ID 4667 — An application client context was deleted
Windows event ID 4668 — An application was initialized
Windows event ID 4670 — Permissions on an object were changed
Windows event ID 4671 — An application attempted to access a blocked ordinal through the TBS
Windows event ID 4672 — Special privileges assigned to new logon
Windows event ID 4673 — A privileged service was called
Windows event ID 4674 — An operation was attempted on a privileged object
Windows event ID 4675 — SIDs were filtered
Windows event ID 4688 — A new process has been created
Windows event ID 4689 — A process has exited
Windows event ID 4690 — An attempt was made to duplicate a handle to an object
Windows event ID 4691 — Indirect access to an object was requested
Windows event ID 4692 — Backup of data protection master key was attempted
Windows event ID 4693 — Recovery of data protection master key was attempted
Windows event ID 4694 — Protection of auditable protected data was attempted
Windows event ID 4695 — Unprotection of auditable protected data was attempted
Windows event ID 4696 — A primary token was assigned to process
Windows event ID 4697 — A service was installed in the system
Windows event ID 4698 — A scheduled task was created
Windows event ID 4699 — A scheduled task was deleted
Windows event ID 4700 — A scheduled task was enabled
Windows event ID 4701 — A scheduled task was disabled
Windows event ID 4702 — A scheduled task was updated
Windows event ID 4704 — A user right was assigned
Windows event ID 4705 — A user right was removed
Windows event ID 4706 — A new trust was created to a domain
Windows event ID 4707 — A trust to a domain was removed
Windows event ID 4709 — IPsec Services was started
Windows event ID 4710 — IPsec Services was disabled
Windows event ID 4711 — PAStore Engine %1
Windows event ID 4712 — IPsec Services encountered a potentially serious failure
Windows event ID 4713 — Kerberos policy was changed
Windows event ID 4714 — Encrypted data recovery policy was changed
Windows event ID 4715 — The audit policy (SACL) on an object was changed
Windows event ID 4716 — Trusted domain information was modified
Windows event ID 4717 — System security access was granted to an account
Windows event ID 4718 — System security access was removed from an account
Windows event ID 4719 — System audit policy was changed
Windows event ID 4720 — A user account was created
Windows event ID 4722 — A user account was enabled
Windows event ID 4723 — An attempt was made to change an account’s password
Windows event ID 4724 — An attempt was made to reset an account’s password
Windows event ID 4725 — A user account was disabled
Windows event ID 4726 — A user account was deleted
Windows event ID 4727 — A security-enabled global group was created
Windows event ID 4728 — A member was added to a security-enabled global group
Windows event ID 4729 — A member was removed from a security-enabled global group
Windows event ID 4730 — A security-enabled global group was deleted
Windows event ID 4731 — A security-enabled local group was created
Windows event ID 4732 — A member was added to a security-enabled local group
Windows event ID 4733 — A member was removed from a security-enabled local group
Windows event ID 4734 — A security-enabled local group was deleted
Windows event ID 4735 — A security-enabled local group was changed
Windows event ID 4737 — A security-enabled global group was changed
Windows event ID 4738 — A user account was changed
Windows event ID 4739 — Domain Policy was changed
Windows event ID 4740 — A user account was locked out
Windows event ID 4741 — A computer account was created
Windows event ID 4742 — A computer account was changed
Windows event ID 4743 — A computer account was deleted
Windows event ID 4744 — A security-disabled local group was created
Windows event ID 4745 — A security-disabled local group was changed
Windows event ID 4746 — A member was added to a security-disabled local group
Windows event ID 4747 — A member was removed from a security-disabled local group
Windows event ID 4748 — A security-disabled local group was deleted
Windows event ID 4749 — A security-disabled global group was created
Windows event ID 4750 — A security-disabled global group was changed
Windows event ID 4751 — A member was added to a security-disabled global group
Windows event ID 4752 — A member was removed from a security-disabled global group
Windows event ID 4753 — A security-disabled global group was deleted
Windows event ID 4754 — A security-enabled universal group was created
Windows event ID 4755 — A security-enabled universal group was changed
Windows event ID 4756 — A member was added to a security-enabled universal group
Windows event ID 4757 — A member was removed from a security-enabled universal group
Windows event ID 4758 — A security-enabled universal group was deleted
Windows event ID 4759 — A security-disabled universal group was created
Windows event ID 4760 — A security-disabled universal group was changed
Windows event ID 4761 — A member was added to a security-disabled universal group
Windows event ID 4762 — A member was removed from a security-disabled universal group
Windows event ID 4763 — A security-disabled universal group was deleted
Windows event ID 4764 — A group’s type was changed
Windows event ID 4765 — SID History was added to an account
Windows event ID 4766 — An attempt to add SID History to an account failed
Windows event ID 4767 — A user account was unlocked
Windows event ID 4768 — A Kerberos authentication ticket (TGT) was requested
Windows event ID 4769 — A Kerberos service ticket was requested
Windows event ID 4770 — A Kerberos service ticket was renewed
Windows event ID 4771 — Kerberos pre-authentication failed
Windows event ID 4772 — A Kerberos authentication ticket request failed
Windows event ID 4773 — A Kerberos service ticket request failed
Windows event ID 4774 — An account was mapped for logon
Windows event ID 4775 — An account could not be mapped for logon
Windows event ID 4776 — The domain controller attempted to validate the credentials for an account
Windows event ID 4777 — The domain controller failed to validate the credentials for an account
Windows event ID 4778 — A session was reconnected to a Window Station
Windows event ID 4779 — A session was disconnected from a Window Station
Windows event ID 4780 — The ACL was set on accounts which are members of administrators groups
Windows event ID 4781 — The name of an account was changed:
Windows event ID 4782 — The password hash an account was accessed
Windows event ID 4783 — A basic application group was created
Windows event ID 4784 — A basic application group was changed
Windows event ID 4785 — A member was added to a basic application group
Windows event ID 4786 — A member was removed from a basic application group
Windows event ID 4787 — A non-member was added to a basic application group
Windows event ID 4788 — A non-member was removed from a basic application group
Windows event ID 4789 — A basic application group was deleted
Windows event ID 4790 — An LDAP query group was created
Windows event ID 4791 — A basic application group was changed
Windows event ID 4792 — An LDAP query group was deleted
Windows event ID 4793 — The Password Policy Checking API was called
Windows event ID 4794 — An attempt was made to set the Directory Services Restore Mode
Windows event ID 4800 — The workstation was locked
Windows event ID 4801 — The workstation was unlocked
Windows event ID 4802 — The screen saver was invoked
Windows event ID 4803 — The screen saver was dismissed
Windows event ID 4816 — RPC detected an integrity violation while decrypting an incoming message
Windows event ID 4817 — Auditing settings on an object were changed
Windows event ID 4864 — A namespace collision was detected
Windows event ID 4865 — A trusted forest information entry was added
Windows event ID 4866 — A trusted forest information entry was removed
Windows event ID 4867 — A trusted forest information entry was modified
Windows event ID 4868 — The certificate manager denied a pending certificate request
Windows event ID 4869 — Certificate Services received a resubmitted certificate request
Windows event ID 4870 — Certificate Services revoked a certificate
Windows event ID 4871 — Certificate Services received a request to publish the certificate revocation list (CRL)
Windows event ID 4872 — Certificate Services published the certificate revocation list (CRL)
Windows event ID 4873 — A certificate request extension changed
Windows event ID 4874 — One or more certificate request attributes changed
Windows event ID 4875 — Certificate Services received a request to shut down
Windows event ID 4876 — Certificate Services backup started
Windows event ID 4877 — Certificate Services backup completed
Windows event ID 4878 — Certificate Services restore started
Windows event ID 4879 — Certificate Services restore completed
Windows event ID 4880 — Certificate Services started
Windows event ID 4881 — Certificate Services stopped
Windows event ID 4882 — The security permissions for Certificate Services changed
Windows event ID 4883 — Certificate Services retrieved an archived key
Windows event ID 4884 — Certificate Services imported a certificate into its database
Windows event ID 4885 — The audit filter for Certificate Services changed
Windows event ID 4886 — Certificate Services received a certificate request
Windows event ID 4887 — Certificate Services approved a certificate request and issued a certificate
Windows event ID 4888 — Certificate Services denied a certificate request
Windows event ID 4889 — Certificate Services set the status of a certificate request to pending
Windows event ID 4890 — The certificate manager settings for Certificate Services changed
Windows event ID 4891 — A configuration entry changed in Certificate Services
Windows event ID 4892 — A property of Certificate Services changed
Windows event ID 4893 — Certificate Services archived a key
Windows event ID 4894 — Certificate Services imported and archived a key
Windows event ID 4895 — Certificate Services published the CA certificate to Active Directory Domain Services
Windows event ID 4896 — One or more rows have been deleted from the certificate database
Windows event ID 4897 — Role separation enabled:
Windows event ID 4898 — Certificate Services loaded a template
Windows event ID 4899 — A Certificate Services template was updated
Windows event ID 4900 — Certificate Services template security was updated
Windows event ID 4902 — The Per-user audit policy table was created
Windows event ID 4904 — An attempt was made to register a security event source
Windows event ID 4905 — An attempt was made to unregister a security event source
Windows event ID 4906 — The CrashOnAuditFail value has changed
Windows event ID 4907 — Auditing settings on object were changed
Windows event ID 4908 — Special Groups Logon table modified
Windows event ID 4909 — The local policy settings for the TBS were changed
Windows event ID 4910 — The group policy settings for the TBS were changed
Windows event ID 4912 — Per User Audit Policy was changed
Windows event ID 4928 — An Active Directory replica source naming context was established
Windows event ID 4929 — An Active Directory replica source naming context was removed
Windows event ID 4930 — An Active Directory replica source naming context was modified
Windows event ID 4931 — An Active Directory replica destination naming context was modified
Windows event ID 4932 — Synchronization of a replica of an Active Directory naming context has begun
Windows event ID 4933 — Synchronization of a replica of an Active Directory naming context has ended
Windows event ID 4934 — Attributes of an Active Directory object were replicated
Windows event ID 4935 — Replication failure begins
Windows event ID 4936 — Replication failure ends
Windows event ID 4937 — A lingering object was removed from a replica
Windows event ID 4944 — The following policy was active when the Windows Firewall started
Windows event ID 4945 — A rule was listed when the Windows Firewall started
Windows event ID 4946 — A change has been made to Windows Firewall exception list. A rule was added
Windows event ID 4947 — A change has been made to Windows Firewall exception list. A rule was modified
Windows event ID 4948 — A change has been made to Windows Firewall exception list. A rule was deleted
Windows event ID 4949 — Windows Firewall settings were restored to the default values
Windows event ID 4950 — A Windows Firewall setting has changed
Windows event ID 4951 — A rule has been ignored because its major version number was not recognized by Windows Firewall
Windows event ID 4952 — Parts of a rule have been ignored because its minor version number was not recognized by Windows Firewall. The other parts of the rule will be enforced
Windows event ID 4953 — A rule has been ignored by Windows Firewall because it could not parse the rule
Windows event ID 4954 — Windows Firewall Group Policy settings have changed. The new settings have been applied
Windows event ID 4956 — Windows Firewall has changed the active profile
Windows event ID 4957 — Windows Firewall did not apply the following rule:
Windows event ID 4958 — Windows Firewall did not apply the following rule because the rule referred to items not configured on this computer:
Windows event ID 4960 — IPsec dropped an inbound packet that failed an integrity check. If this problem persists, it could indicate a network issue or that packets are being modified in transit to this computer. Verify that the packets sent from the remot
Windows event ID 4961 — IPsec dropped an inbound packet that failed a replay check. If this problem persists, it could indicate a replay attack against this computer
Windows event ID 4962 — IPsec dropped an inbound packet that failed a replay check. The inbound packet had too low a sequence number to ensure it was not a replay
Windows event ID 4963 — IPsec dropped an inbound clear text packet that should have been secured. This is usually due to the remote computer changing its IPsec policy without informing this computer. This could also be a spoofing attack attempt
Windows event ID 4964 — Special groups have been assigned to a new logon
Windows event ID 4965 — IPsec received a packet from a remote computer with an incorrect Security Parameter Index (SPI). This is usually caused by malfunctioning hardware that is corrupting packets. If these errors persist, verify that the packets sent fr
Windows event ID 4976 — IPsec received an invalid negotiation packet
Windows event ID 4977 — IPsec received an invalid negotiation packet
Windows event ID 4978 — IPsec received an invalid negotiation packet
Windows event ID 4979 — IPsec Main Mode and Extended Mode security associations were established
Windows event ID 4980 — IPsec Main Mode and Extended Mode security associations were established
Windows event ID 4981 — IPsec Main Mode and Extended Mode security associations were established
Windows event ID 4982 — IPsec Main Mode and Extended Mode security associations were established
Windows event ID 4983 — An IPsec Extended Mode negotiation failed
Windows event ID 4984 — An IPsec Extended Mode negotiation failed
Windows event ID 4985 — The state of a transaction has changed
Windows event ID 5024 — The Windows Firewall Service has started successfully
Windows event ID 5025 — The Windows Firewall Service has been stopped
Windows event ID 5027 — The Windows Firewall Service was unable to retrieve the security policy from the local storage. The service will continue enforcing the current policy
Windows event ID 5028 — The Windows Firewall Service was unable to parse the new security policy. The service will continue with currently enforced policy
Windows event ID 5029 — The Windows Firewall Service failed to initialize the driver. The service will continue to enforce the current policy
Windows event ID 5030 — The Windows Firewall Service failed to start
Windows event ID 5031 — The Windows Firewall Service blocked an application from accepting incoming connections on the network
Windows event ID 5032 — Windows Firewall was unable to notify the user that it blocked an application from accepting incoming connections on the network
Windows event ID 5033 — The Windows Firewall Driver has started successfully
Windows event ID 5034 — The Windows Firewall Driver has been stopped
Windows event ID 5035 — The Windows Firewall Driver failed to start
Windows event ID 5037 — The Windows Firewall Driver detected critical runtime error. Terminating
Windows event ID 5038 — Code integrity determined that the image hash of a file is not valid. The file could be corrupt due to unauthorized modification or the invalid hash could indicate a potential disk device error
Windows event ID 5039 — A registry key was virtualized
Windows event ID 5040 — IPsec: An Authentication Set was added
Windows event ID 5041 — IPsec: An Authentication Set was modified
Windows event ID 5042 — IPsec: An Authentication Set was deleted
Windows event ID 5043 — IPsec: A Connection Security Rule was added
Windows event ID 5044 — IPsec: A Connection Security Rule was modified
Windows event ID 5045 — IPsec: A Connection Security Rule was deleted
Windows event ID 5046 — IPsec: A Crypto Set was added
Windows event ID 5047 — IPsec: A Crypto Set was modified
Windows event ID 5048 — IPsec: A Crypto Set was deleted
Windows event ID 5049 — An IPsec Security Association was deleted
Windows event ID 5050 — An attempt to programmatically disable the Windows Firewall using a call to INetFwProfile.FirewallEnabled(FALSE) interface was rejected because this API is not supported on Windows Vista
Windows event ID 5051 — A file was virtualized
Windows event ID 5056 — A cryptographic self test was performed
Windows event ID 5057 — A cryptographic primitive operation failed
Windows event ID 5058 — Key file operation
Windows event ID 5059 — Key migration operation
Windows event ID 5060 — Verification operation failed
Windows event ID 5061 — Cryptographic operation
Windows event ID 5062 — A kernel-mode cryptographic self test was performed
Windows event ID 5063 — A cryptographic provider operation was attempted
Windows event ID 5064 — A cryptographic context operation was attempted
Windows event ID 5065 — A cryptographic context modification was attempted
Windows event ID 5066 — A cryptographic function operation was attempted
Windows event ID 5067 — A cryptographic function modification was attempted
Windows event ID 5068 — A cryptographic function provider operation was attempted
Windows event ID 5069 — A cryptographic function property operation was attempted
Windows event ID 5070 — A cryptographic function property modification was attempted
Windows event ID 5120 — OCSP Responder Service Started
Windows event ID 5121 — OCSP Responder Service Stopped
Windows event ID 5122 — A Configuration entry changed in the OCSP Responder Service
Windows event ID 5123 — A configuration entry changed in the OCSP Responder Service
Windows event ID 5124 — A security setting was updated on OCSP Responder Service
Windows event ID 5125 — A request was submitted to OCSP Responder Service
Windows event ID 5126 — Signing Certificate was automatically updated by the OCSP Responder Service
Windows event ID 5127 — The OCSP Revocation Provider successfully updated the revocation information
Windows event ID 5136 — A directory service object was modified
Windows event ID 5137 — A directory service object was created
Windows event ID 5138 — A directory service object was undeleted
Windows event ID 5139 — A directory service object was moved
Windows event ID 5140 — A network share object was accessed
Windows event ID 5141 — A directory service object was deleted
Windows event ID 5142 — A network share object was added
Windows event ID 5143 — A network share object was modified
Windows event ID 5144 — A network share object was deleted
Windows event ID 5145 — A network share object was checked to see whether the client can be granted desired access
Windows event ID 5148 — The Windows Filtering Platform has detected a DoS attack and entered a defensive mode; packets associated with this attack will be discarded
Windows event ID 5149 — The DoS attack has subsided and normal processing is being resumed
Windows event ID 5150 — The Windows Filtering Platform has blocked a packet
Windows event ID 5151 — A more restrictive Windows Filtering Platform filter has blocked a packet
Windows event ID 5152 — The Windows Filtering Platform blocked a packet
Windows event ID 5153 — A more restrictive Windows Filtering Platform filter has blocked a packet
Windows event ID 5154 — The Windows Filtering Platform has permitted an application or service to listen on a port for incoming connections
Windows event ID 5155 — The Windows Filtering Platform has blocked an application or service from listening on a port for incoming connections
Windows event ID 5156 — The Windows Filtering Platform has allowed a connection
Windows event ID 5157 — The Windows Filtering Platform has blocked a connection
Windows event ID 5158 — The Windows Filtering Platform has permitted a bind to a local port
Windows event ID 5159 — The Windows Filtering Platform has blocked a bind to a local port
Windows event ID 5168 — Spn check for SMB/SMB2 failed
Windows event ID 5376 — Credential Manager credentials were backed up
Windows event ID 5377 — Credential Manager credentials were restored from a backup
Windows event ID 5378 — The requested credentials delegation was disallowed by policy
Windows event ID 5440 — The following callout was present when the Windows Filtering Platform Base Filtering Engine started
Windows event ID 5441 — The following filter was present when the Windows Filtering Platform Base Filtering Engine started
Windows event ID 5442 — The following provider was present when the Windows Filtering Platform Base Filtering Engine started
Windows event ID 5443 — The following provider context was present when the Windows Filtering Platform Base Filtering Engine started
Windows event ID 5444 — The following sub-layer was present when the Windows Filtering Platform Base Filtering Engine started
Windows event ID 5446 — A Windows Filtering Platform callout has been changed
Windows event ID 5447 — A Windows Filtering Platform filter has been changed
Windows event ID 5448 — A Windows Filtering Platform provider has been changed
Windows event ID 5449 — A Windows Filtering Platform provider context has been changed
Windows event ID 5450 — A Windows Filtering Platform sub-layer has been changed
Windows event ID 5451 — An IPsec Quick Mode security association was established
Windows event ID 5452 — An IPsec Quick Mode security association ended
Windows event ID 5453 — An IPsec negotiation with a remote computer failed because the IKE and AuthIP IPsec Keying Modules (IKEEXT) service is not started
Windows event ID 5456 — PAStore Engine applied Active Directory storage IPsec policy on the computer
Windows event ID 5457 — PAStore Engine failed to apply Active Directory storage IPsec policy on the computer
Windows event ID 5458 — PAStore Engine applied locally cached copy of Active Directory storage IPsec policy on the computer
Windows event ID 5459 — PAStore Engine failed to apply locally cached copy of Active Directory storage IPsec policy on the computer
Windows event ID 5460 — PAStore Engine applied local registry storage IPsec policy on the computer
Windows event ID 5461 — PAStore Engine failed to apply local registry storage IPsec policy on the computer
Windows event ID 5462 — PAStore Engine failed to apply some rules of the active IPsec policy on the computer. Use the IP Security Monitor snap-in to diagnose the problem
Windows event ID 5463 — PAStore Engine polled for changes to the active IPsec policy and detected no changes
Windows event ID 5464 — PAStore Engine polled for changes to the active IPsec policy, detected changes, and applied them to IPsec Services
Windows event ID 5465 — PAStore Engine received a control for forced reloading of IPsec policy and processed the control successfully
Windows event ID 5466 — PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory cannot be reached, and will use the cached copy of the Active Directory IPsec policy instead. Any changes made to the Active D
Windows event ID 5467 — PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory can be reached, and found no changes to the policy. The cached copy of the Active Directory IPsec policy is no longer being us
Windows event ID 5468 — PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory can be reached, found changes to the policy, and applied those changes. The cached copy of the Active Directory IPsec policy i
Windows event ID 5471 — PAStore Engine loaded local storage IPsec policy on the computer
Windows event ID 5472 — PAStore Engine failed to load local storage IPsec policy on the computer
Windows event ID 5473 — PAStore Engine loaded directory storage IPsec policy on the computer
Windows event ID 5474 — PAStore Engine failed to load directory storage IPsec policy on the computer
Windows event ID 5477 — PAStore Engine failed to add quick mode filter
Windows event ID 5478 — IPsec Services has started successfully
Windows event ID 5479 — IPsec Services has been shut down successfully. The shutdown of IPsec Services can put the computer at greater risk of network attack or expose the computer to potential security risks
Windows event ID 5480 — IPsec Services failed to get the complete list of network interfaces on the computer. This poses a potential security risk because some of the network interfaces may not get the protection provided by the applied IPsec filters. Use
Windows event ID 5483 — IPsec Services failed to initialize RPC server. IPsec Services could not be started
Windows event ID 5484 — IPsec Services has experienced a critical failure and has been shut down. The shutdown of IPsec Services can put the computer at greater risk of network attack or expose the computer to potential security risks
Windows event ID 5485 — IPsec Services failed to process some IPsec filters on a plug-and-play event for network interfaces. This poses a potential security risk because some of the network interfaces may not get the protection provided by the applied IPs
Windows event ID 5632 — A request was made to authenticate to a wireless network
Windows event ID 5633 — A request was made to authenticate to a wired network
Windows event ID 5712 — A Remote Procedure Call (RPC) was attempted
Windows event ID 5888 — An object in the COM+ Catalog was modified
Windows event ID 5889 — An object was deleted from the COM+ Catalog
Windows event ID 5890 — An object was added to the COM+ Catalog
Windows event ID 6144 — Security policy in the group policy objects has been applied successfully
Windows event ID 6145 — One or more errors occurred while processing security policy in the group policy objects
Windows event ID 6272 — Network Policy Server granted access to a user
Windows event ID 6273 — Network Policy Server denied access to a user
Windows event ID 6274 — Network Policy Server discarded the request for a user
Windows event ID 6275 — Network Policy Server discarded the accounting request for a user
Windows event ID 6276 — Network Policy Server quarantined a user
Windows event ID 6277 — Network Policy Server granted access to a user but put it on probation because the host did not meet the defined health policy
Windows event ID 6278 — Network Policy Server granted full access to a user because the host met the defined health policy
Windows event ID 6279 — Network Policy Server locked the user account due to repeated failed authentication attempts
Windows event ID 6280 — Network Policy Server unlocked the user account
Windows event ID 6281 — Code Integrity determined that the page hashes of an image file are not valid. The file could be improperly signed without page hashes or corrupt due to unauthorized modification. The invalid hashes could indicate a potential disk
Windows event ID 6400 — BranchCache: Received an incorrectly formatted response while discovering availability of content.
Windows event ID 6401 — BranchCache: Received invalid data from a peer. Data discarded.
Windows event ID 6402 — BranchCache: The message to the hosted cache offering it data is incorrectly formatted.
Windows event ID 6403 — BranchCache: The hosted cache sent an incorrectly formatted response to the client
Windows event ID 6404 — BranchCache: Hosted cache could not be authenticated using the provisioned SSL certificate.
Windows event ID 6405 — BranchCache: %2 instance(s) of event id %1 occurred
Windows event ID 6406 — %1 registered to Windows Firewall to control filtering for the following: %2
Windows event ID 6407 — 1%
Windows event ID 6408 — Registered product %1 failed and Windows Firewall is now controlling the filtering for %2
Windows event ID 8191 — Highest System-Defined Audit Message Value
| Windows |
1100 |
The event logging service has shut down |
| Windows |
1101 |
Audit events have been dropped by the transport. |
| Windows |
1102 |
The audit log was cleared |
| Windows |
1104 |
The security Log is now full |
| Windows |
1105 |
Event log automatic backup |
| Windows |
1108 |
The event logging service encountered an error |
| Windows |
4608 |
Windows is starting up |
| Windows |
4609 |
Windows is shutting down |
| Windows |
4610 |
An authentication package has been loaded by the Local Security Authority |
| Windows |
4611 |
A trusted logon process has been registered with the Local Security Authority |
| Windows |
4612 |
Internal resources allocated for the queuing of audit messages have been exhausted, leading to the loss of some audits. |
| Windows |
4614 |
A notification package has been loaded by the Security Account Manager. |
| Windows |
4615 |
Invalid use of LPC port |
| Windows |
4616 |
The system time was changed. |
| Windows |
4618 |
A monitored security event pattern has occurred |
| Windows |
4621 |
Administrator recovered system from CrashOnAuditFail |
| Windows |
4622 |
A security package has been loaded by the Local Security Authority. |
| Windows |
4624 |
An account was successfully logged on |
| Windows |
4625 |
An account failed to log on |
| Windows |
4626 |
User/Device claims information |
| Windows |
4627 |
Group membership information. |
| Windows |
4634 |
An account was logged off |
| Windows |
4646 |
IKE DoS-prevention mode started |
| Windows |
4647 |
User initiated logoff |
| Windows |
4648 |
A logon was attempted using explicit credentials |
| Windows |
4649 |
A replay attack was detected |
| Windows |
4650 |
An IPsec Main Mode security association was established |
| Windows |
4651 |
An IPsec Main Mode security association was established |
| Windows |
4652 |
An IPsec Main Mode negotiation failed |
| Windows |
4653 |
An IPsec Main Mode negotiation failed |
| Windows |
4654 |
An IPsec Quick Mode negotiation failed |
| Windows |
4655 |
An IPsec Main Mode security association ended |
| Windows |
4656 |
A handle to an object was requested |
| Windows |
4657 |
A registry value was modified |
| Windows |
4658 |
The handle to an object was closed |
| Windows |
4659 |
A handle to an object was requested with intent to delete |
| Windows |
4660 |
An object was deleted |
| Windows |
4661 |
A handle to an object was requested |
| Windows |
4662 |
An operation was performed on an object |
| Windows |
4663 |
An attempt was made to access an object |
| Windows |
4664 |
An attempt was made to create a hard link |
| Windows |
4665 |
An attempt was made to create an application client context. |
| Windows |
4666 |
An application attempted an operation |
| Windows |
4667 |
An application client context was deleted |
| Windows |
4668 |
An application was initialized |
| Windows |
4670 |
Permissions on an object were changed |
| Windows |
4671 |
An application attempted to access a blocked ordinal through the TBS |
| Windows |
4672 |
Special privileges assigned to new logon |
| Windows |
4673 |
A privileged service was called |
| Windows |
4674 |
An operation was attempted on a privileged object |
| Windows |
4675 |
SIDs were filtered |
| Windows |
4688 |
A new process has been created |
| Windows |
4689 |
A process has exited |
| Windows |
4690 |
An attempt was made to duplicate a handle to an object |
| Windows |
4691 |
Indirect access to an object was requested |
| Windows |
4692 |
Backup of data protection master key was attempted |
| Windows |
4693 |
Recovery of data protection master key was attempted |
| Windows |
4694 |
Protection of auditable protected data was attempted |
| Windows |
4695 |
Unprotection of auditable protected data was attempted |
| Windows |
4696 |
A primary token was assigned to process |
| Windows |
4697 |
A service was installed in the system |
| Windows |
4698 |
A scheduled task was created |
| Windows |
4699 |
A scheduled task was deleted |
| Windows |
4700 |
A scheduled task was enabled |
| Windows |
4701 |
A scheduled task was disabled |
| Windows |
4702 |
A scheduled task was updated |
| Windows |
4703 |
A token right was adjusted |
| Windows |
4704 |
A user right was assigned |
| Windows |
4705 |
A user right was removed |
| Windows |
4706 |
A new trust was created to a domain |
| Windows |
4707 |
A trust to a domain was removed |
| Windows |
4709 |
IPsec Services was started |
| Windows |
4710 |
IPsec Services was disabled |
| Windows |
4711 |
PAStore Engine (1%) |
| Windows |
4712 |
IPsec Services encountered a potentially serious failure |
| Windows |
4713 |
Kerberos policy was changed |
| Windows |
4714 |
Encrypted data recovery policy was changed |
| Windows |
4715 |
The audit policy (SACL) on an object was changed |
| Windows |
4716 |
Trusted domain information was modified |
| Windows |
4717 |
System security access was granted to an account |
| Windows |
4718 |
System security access was removed from an account |
| Windows |
4719 |
System audit policy was changed |
| Windows |
4720 |
A user account was created |
| Windows |
4722 |
A user account was enabled |
| Windows |
4723 |
An attempt was made to change an account’s password |
| Windows |
4724 |
An attempt was made to reset an accounts password |
| Windows |
4725 |
A user account was disabled |
| Windows |
4726 |
A user account was deleted |
| Windows |
4727 |
A security-enabled global group was created |
| Windows |
4728 |
A member was added to a security-enabled global group |
| Windows |
4729 |
A member was removed from a security-enabled global group |
| Windows |
4730 |
A security-enabled global group was deleted |
| Windows |
4731 |
A security-enabled local group was created |
| Windows |
4732 |
A member was added to a security-enabled local group |
| Windows |
4733 |
A member was removed from a security-enabled local group |
| Windows |
4734 |
A security-enabled local group was deleted |
| Windows |
4735 |
A security-enabled local group was changed |
| Windows |
4737 |
A security-enabled global group was changed |
| Windows |
4738 |
A user account was changed |
| Windows |
4739 |
Domain Policy was changed |
| Windows |
4740 |
A user account was locked out |
| Windows |
4741 |
A computer account was created |
| Windows |
4742 |
A computer account was changed |
| Windows |
4743 |
A computer account was deleted |
| Windows |
4744 |
A security-disabled local group was created |
| Windows |
4745 |
A security-disabled local group was changed |
| Windows |
4746 |
A member was added to a security-disabled local group |
| Windows |
4747 |
A member was removed from a security-disabled local group |
| Windows |
4748 |
A security-disabled local group was deleted |
| Windows |
4749 |
A security-disabled global group was created |
| Windows |
4750 |
A security-disabled global group was changed |
| Windows |
4751 |
A member was added to a security-disabled global group |
| Windows |
4752 |
A member was removed from a security-disabled global group |
| Windows |
4753 |
A security-disabled global group was deleted |
| Windows |
4754 |
A security-enabled universal group was created |
| Windows |
4755 |
A security-enabled universal group was changed |
| Windows |
4756 |
A member was added to a security-enabled universal group |
| Windows |
4757 |
A member was removed from a security-enabled universal group |
| Windows |
4758 |
A security-enabled universal group was deleted |
| Windows |
4759 |
A security-disabled universal group was created |
| Windows |
4760 |
A security-disabled universal group was changed |
| Windows |
4761 |
A member was added to a security-disabled universal group |
| Windows |
4762 |
A member was removed from a security-disabled universal group |
| Windows |
4763 |
A security-disabled universal group was deleted |
| Windows |
4764 |
A groups type was changed |
| Windows |
4765 |
SID History was added to an account |
| Windows |
4766 |
An attempt to add SID History to an account failed |
| Windows |
4767 |
A user account was unlocked |
| Windows |
4768 |
A Kerberos authentication ticket (TGT) was requested |
| Windows |
4769 |
A Kerberos service ticket was requested |
| Windows |
4770 |
A Kerberos service ticket was renewed |
| Windows |
4771 |
Kerberos pre-authentication failed |
| Windows |
4772 |
A Kerberos authentication ticket request failed |
| Windows |
4773 |
A Kerberos service ticket request failed |
| Windows |
4774 |
An account was mapped for logon |
| Windows |
4775 |
An account could not be mapped for logon |
| Windows |
4776 |
The domain controller attempted to validate the credentials for an account |
| Windows |
4777 |
The domain controller failed to validate the credentials for an account |
| Windows |
4778 |
A session was reconnected to a Window Station |
| Windows |
4779 |
A session was disconnected from a Window Station |
| Windows |
4780 |
The ACL was set on accounts which are members of administrators groups |
| Windows |
4781 |
The name of an account was changed |
| Windows |
4782 |
The password hash an account was accessed |
| Windows |
4783 |
A basic application group was created |
| Windows |
4784 |
A basic application group was changed |
| Windows |
4785 |
A member was added to a basic application group |
| Windows |
4786 |
A member was removed from a basic application group |
| Windows |
4787 |
A non-member was added to a basic application group |
| Windows |
4788 |
A non-member was removed from a basic application group.. |
| Windows |
4789 |
A basic application group was deleted |
| Windows |
4790 |
An LDAP query group was created |
| Windows |
4791 |
A basic application group was changed |
| Windows |
4792 |
An LDAP query group was deleted |
| Windows |
4793 |
The Password Policy Checking API was called |
| Windows |
4794 |
An attempt was made to set the Directory Services Restore Mode administrator password |
| Windows |
4797 |
An attempt was made to query the existence of a blank password for an account |
| Windows |
4798 |
A user’s local group membership was enumerated. |
| Windows |
4799 |
A security-enabled local group membership was enumerated |
| Windows |
4800 |
The workstation was locked |
| Windows |
4801 |
The workstation was unlocked |
| Windows |
4802 |
The screen saver was invoked |
| Windows |
4803 |
The screen saver was dismissed |
| Windows |
4816 |
RPC detected an integrity violation while decrypting an incoming message |
| Windows |
4817 |
Auditing settings on object were changed. |
| Windows |
4818 |
Proposed Central Access Policy does not grant the same access permissions as the current Central Access Policy |
| Windows |
4819 |
Central Access Policies on the machine have been changed |
| Windows |
4820 |
A Kerberos Ticket-granting-ticket (TGT) was denied because the device does not meet the access control restrictions |
| Windows |
4821 |
A Kerberos service ticket was denied because the user, device, or both does not meet the access control restrictions |
| Windows |
4822 |
NTLM authentication failed because the account was a member of the Protected User group |
| Windows |
4823 |
NTLM authentication failed because access control restrictions are required |
| Windows |
4824 |
Kerberos preauthentication by using DES or RC4 failed because the account was a member of the Protected User group |
| Windows |
4825 |
A user was denied the access to Remote Desktop. By default, users are allowed to connect only if they are members of the Remote Desktop Users group or Administrators group |
| Windows |
4826 |
Boot Configuration Data loaded |
| Windows |
4830 |
SID History was removed from an account |
| Windows |
4864 |
A namespace collision was detected |
| Windows |
4865 |
A trusted forest information entry was added |
| Windows |
4866 |
A trusted forest information entry was removed |
| Windows |
4867 |
A trusted forest information entry was modified |
| Windows |
4868 |
The certificate manager denied a pending certificate request |
| Windows |
4869 |
Certificate Services received a resubmitted certificate request |
| Windows |
4870 |
Certificate Services revoked a certificate |
| Windows |
4871 |
Certificate Services received a request to publish the certificate revocation list (CRL) |
| Windows |
4872 |
Certificate Services published the certificate revocation list (CRL) |
| Windows |
4873 |
A certificate request extension changed |
| Windows |
4874 |
One or more certificate request attributes changed. |
| Windows |
4875 |
Certificate Services received a request to shut down |
| Windows |
4876 |
Certificate Services backup started |
| Windows |
4877 |
Certificate Services backup completed |
| Windows |
4878 |
Certificate Services restore started |
| Windows |
4879 |
Certificate Services restore completed |
| Windows |
4880 |
Certificate Services started |
| Windows |
4881 |
Certificate Services stopped |
| Windows |
4882 |
The security permissions for Certificate Services changed |
| Windows |
4883 |
Certificate Services retrieved an archived key |
| Windows |
4884 |
Certificate Services imported a certificate into its database |
| Windows |
4885 |
The audit filter for Certificate Services changed |
| Windows |
4886 |
Certificate Services received a certificate request |
| Windows |
4887 |
Certificate Services approved a certificate request and issued a certificate |
| Windows |
4888 |
Certificate Services denied a certificate request |
| Windows |
4889 |
Certificate Services set the status of a certificate request to pending |
| Windows |
4890 |
The certificate manager settings for Certificate Services changed. |
| Windows |
4891 |
A configuration entry changed in Certificate Services |
| Windows |
4892 |
A property of Certificate Services changed |
| Windows |
4893 |
Certificate Services archived a key |
| Windows |
4894 |
Certificate Services imported and archived a key |
| Windows |
4895 |
Certificate Services published the CA certificate to Active Directory Domain Services |
| Windows |
4896 |
One or more rows have been deleted from the certificate database |
| Windows |
4897 |
Role separation enabled |
| Windows |
4898 |
Certificate Services loaded a template |
| Windows |
4899 |
A Certificate Services template was updated |
| Windows |
4900 |
Certificate Services template security was updated |
| Windows |
4902 |
The Per-user audit policy table was created |
| Windows |
4904 |
An attempt was made to register a security event source |
| Windows |
4905 |
An attempt was made to unregister a security event source |
| Windows |
4906 |
The CrashOnAuditFail value has changed |
| Windows |
4907 |
Auditing settings on object were changed |
| Windows |
4908 |
Special Groups Logon table modified |
| Windows |
4909 |
The local policy settings for the TBS were changed |
| Windows |
4910 |
The group policy settings for the TBS were changed |
| Windows |
4911 |
Resource attributes of the object were changed |
| Windows |
4912 |
Per User Audit Policy was changed |
| Windows |
4913 |
Central Access Policy on the object was changed |
| Windows |
4928 |
An Active Directory replica source naming context was established |
| Windows |
4929 |
An Active Directory replica source naming context was removed |
| Windows |
4930 |
An Active Directory replica source naming context was modified |
| Windows |
4931 |
An Active Directory replica destination naming context was modified |
| Windows |
4932 |
Synchronization of a replica of an Active Directory naming context has begun |
| Windows |
4933 |
Synchronization of a replica of an Active Directory naming context has ended |
| Windows |
4934 |
Attributes of an Active Directory object were replicated |
| Windows |
4935 |
Replication failure begins |
| Windows |
4936 |
Replication failure ends |
| Windows |
4937 |
A lingering object was removed from a replica |
| Windows |
4944 |
The following policy was active when the Windows Firewall started |
| Windows |
4945 |
A rule was listed when the Windows Firewall started |
| Windows |
4946 |
A change has been made to Windows Firewall exception list. A rule was added |
| Windows |
4947 |
A change has been made to Windows Firewall exception list. A rule was modified |
| Windows |
4948 |
A change has been made to Windows Firewall exception list. A rule was deleted |
| Windows |
4949 |
Windows Firewall settings were restored to the default values |
| Windows |
4950 |
A Windows Firewall setting has changed |
| Windows |
4951 |
A rule has been ignored because its major version number was not recognized by Windows Firewall |
| Windows |
4952 |
Parts of a rule have been ignored because its minor version number was not recognized by Windows Firewall |
| Windows |
4953 |
A rule has been ignored by Windows Firewall because it could not parse the rule |
| Windows |
4954 |
Windows Firewall Group Policy settings has changed. The new settings have been applied |
| Windows |
4956 |
Windows Firewall has changed the active profile |
| Windows |
4957 |
Windows Firewall did not apply the following rule |
| Windows |
4958 |
Windows Firewall did not apply the following rule because the rule referred to items not configured on this computer |
| Windows |
4960 |
IPsec dropped an inbound packet that failed an integrity check |
| Windows |
4961 |
IPsec dropped an inbound packet that failed a replay check |
| Windows |
4962 |
IPsec dropped an inbound packet that failed a replay check |
| Windows |
4963 |
IPsec dropped an inbound clear text packet that should have been secured |
| Windows |
4964 |
Special groups have been assigned to a new logon |
| Windows |
4965 |
IPsec received a packet from a remote computer with an incorrect Security Parameter Index (SPI). |
| Windows |
4976 |
During Main Mode negotiation, IPsec received an invalid negotiation packet. |
| Windows |
4977 |
During Quick Mode negotiation, IPsec received an invalid negotiation packet. |
| Windows |
4978 |
During Extended Mode negotiation, IPsec received an invalid negotiation packet. |
| Windows |
4979 |
IPsec Main Mode and Extended Mode security associations were established. |
| Windows |
4980 |
IPsec Main Mode and Extended Mode security associations were established |
| Windows |
4981 |
IPsec Main Mode and Extended Mode security associations were established |
| Windows |
4982 |
IPsec Main Mode and Extended Mode security associations were established |
| Windows |
4983 |
An IPsec Extended Mode negotiation failed |
| Windows |
4984 |
An IPsec Extended Mode negotiation failed |
| Windows |
4985 |
The state of a transaction has changed |
| Windows |
5024 |
The Windows Firewall Service has started successfully |
| Windows |
5025 |
The Windows Firewall Service has been stopped |
| Windows |
5027 |
The Windows Firewall Service was unable to retrieve the security policy from the local storage |
| Windows |
5028 |
The Windows Firewall Service was unable to parse the new security policy. |
| Windows |
5029 |
The Windows Firewall Service failed to initialize the driver |
| Windows |
5030 |
The Windows Firewall Service failed to start |
| Windows |
5031 |
The Windows Firewall Service blocked an application from accepting incoming connections on the network. |
| Windows |
5032 |
Windows Firewall was unable to notify the user that it blocked an application from accepting incoming connections on the network |
| Windows |
5033 |
The Windows Firewall Driver has started successfully |
| Windows |
5034 |
The Windows Firewall Driver has been stopped |
| Windows |
5035 |
The Windows Firewall Driver failed to start |
| Windows |
5037 |
The Windows Firewall Driver detected critical runtime error. Terminating |
| Windows |
5038 |
Code integrity determined that the image hash of a file is not valid |
| Windows |
5039 |
A registry key was virtualized. |
| Windows |
5040 |
A change has been made to IPsec settings. An Authentication Set was added. |
| Windows |
5041 |
A change has been made to IPsec settings. An Authentication Set was modified |
| Windows |
5042 |
A change has been made to IPsec settings. An Authentication Set was deleted |
| Windows |
5043 |
A change has been made to IPsec settings. A Connection Security Rule was added |
| Windows |
5044 |
A change has been made to IPsec settings. A Connection Security Rule was modified |
| Windows |
5045 |
A change has been made to IPsec settings. A Connection Security Rule was deleted |
| Windows |
5046 |
A change has been made to IPsec settings. A Crypto Set was added |
| Windows |
5047 |
A change has been made to IPsec settings. A Crypto Set was modified |
| Windows |
5048 |
A change has been made to IPsec settings. A Crypto Set was deleted |
| Windows |
5049 |
An IPsec Security Association was deleted |
| Windows |
5050 |
An attempt to programmatically disable the Windows Firewall using a call to INetFwProfile.FirewallEnabled(FALSE |
| Windows |
5051 |
A file was virtualized |
| Windows |
5056 |
A cryptographic self test was performed |
| Windows |
5057 |
A cryptographic primitive operation failed |
| Windows |
5058 |
Key file operation |
| Windows |
5059 |
Key migration operation |
| Windows |
5060 |
Verification operation failed |
| Windows |
5061 |
Cryptographic operation |
| Windows |
5062 |
A kernel-mode cryptographic self test was performed |
| Windows |
5063 |
A cryptographic provider operation was attempted |
| Windows |
5064 |
A cryptographic context operation was attempted |
| Windows |
5065 |
A cryptographic context modification was attempted |
| Windows |
5066 |
A cryptographic function operation was attempted |
| Windows |
5067 |
A cryptographic function modification was attempted |
| Windows |
5068 |
A cryptographic function provider operation was attempted |
| Windows |
5069 |
A cryptographic function property operation was attempted |
| Windows |
5070 |
A cryptographic function property operation was attempted |
| Windows |
5071 |
Key access denied by Microsoft key distribution service |
| Windows |
5120 |
OCSP Responder Service Started |
| Windows |
5121 |
OCSP Responder Service Stopped |
| Windows |
5122 |
A Configuration entry changed in the OCSP Responder Service |
| Windows |
5123 |
A configuration entry changed in the OCSP Responder Service |
| Windows |
5124 |
A security setting was updated on OCSP Responder Service |
| Windows |
5125 |
A request was submitted to OCSP Responder Service |
| Windows |
5126 |
Signing Certificate was automatically updated by the OCSP Responder Service |
| Windows |
5127 |
The OCSP Revocation Provider successfully updated the revocation information |
| Windows |
5136 |
A directory service object was modified |
| Windows |
5137 |
A directory service object was created |
| Windows |
5138 |
A directory service object was undeleted |
| Windows |
5139 |
A directory service object was moved |
| Windows |
5140 |
A network share object was accessed |
| Windows |
5141 |
A directory service object was deleted |
| Windows |
5142 |
A network share object was added. |
| Windows |
5143 |
A network share object was modified |
| Windows |
5144 |
A network share object was deleted. |
| Windows |
5145 |
A network share object was checked to see whether client can be granted desired access |
| Windows |
5146 |
The Windows Filtering Platform has blocked a packet |
| Windows |
5147 |
A more restrictive Windows Filtering Platform filter has blocked a packet |
| Windows |
5148 |
The Windows Filtering Platform has detected a DoS attack and entered a defensive mode; packets associated with this attack will be discarded. |
| Windows |
5149 |
The DoS attack has subsided and normal processing is being resumed. |
| Windows |
5150 |
The Windows Filtering Platform has blocked a packet. |
| Windows |
5151 |
A more restrictive Windows Filtering Platform filter has blocked a packet. |
| Windows |
5152 |
The Windows Filtering Platform blocked a packet |
| Windows |
5153 |
A more restrictive Windows Filtering Platform filter has blocked a packet |
| Windows |
5154 |
The Windows Filtering Platform has permitted an application or service to listen on a port for incoming connections |
| Windows |
5155 |
The Windows Filtering Platform has blocked an application or service from listening on a port for incoming connections |
| Windows |
5156 |
The Windows Filtering Platform has allowed a connection |
| Windows |
5157 |
The Windows Filtering Platform has blocked a connection |
| Windows |
5158 |
The Windows Filtering Platform has permitted a bind to a local port |
| Windows |
5159 |
The Windows Filtering Platform has blocked a bind to a local port |
| Windows |
5168 |
Spn check for SMB/SMB2 fails. |
| Windows |
5169 |
A directory service object was modified |
| Windows |
5170 |
A directory service object was modified during a background cleanup task |
| Windows |
5376 |
Credential Manager credentials were backed up |
| Windows |
5377 |
Credential Manager credentials were restored from a backup |
| Windows |
5378 |
The requested credentials delegation was disallowed by policy |
| Windows |
5379 |
Credential Manager credentials were read |
| Windows |
5380 |
Vault Find Credential |
| Windows |
5381 |
Vault credentials were read |
| Windows |
5382 |
Vault credentials were read |
| Windows |
5440 |
The following callout was present when the Windows Filtering Platform Base Filtering Engine started |
| Windows |
5441 |
The following filter was present when the Windows Filtering Platform Base Filtering Engine started |
| Windows |
5442 |
The following provider was present when the Windows Filtering Platform Base Filtering Engine started |
| Windows |
5443 |
The following provider context was present when the Windows Filtering Platform Base Filtering Engine started |
| Windows |
5444 |
The following sub-layer was present when the Windows Filtering Platform Base Filtering Engine started |
| Windows |
5446 |
A Windows Filtering Platform callout has been changed |
| Windows |
5447 |
A Windows Filtering Platform filter has been changed |
| Windows |
5448 |
A Windows Filtering Platform provider has been changed |
| Windows |
5449 |
A Windows Filtering Platform provider context has been changed |
| Windows |
5450 |
A Windows Filtering Platform sub-layer has been changed |
| Windows |
5451 |
An IPsec Quick Mode security association was established |
| Windows |
5452 |
An IPsec Quick Mode security association ended |
| Windows |
5453 |
An IPsec negotiation with a remote computer failed because the IKE and AuthIP IPsec Keying Modules (IKEEXT) service is not started |
| Windows |
5456 |
PAStore Engine applied Active Directory storage IPsec policy on the computer |
| Windows |
5457 |
PAStore Engine failed to apply Active Directory storage IPsec policy on the computer |
| Windows |
5458 |
PAStore Engine applied locally cached copy of Active Directory storage IPsec policy on the computer |
| Windows |
5459 |
PAStore Engine failed to apply locally cached copy of Active Directory storage IPsec policy on the computer |
| Windows |
5460 |
PAStore Engine applied local registry storage IPsec policy on the computer |
| Windows |
5461 |
PAStore Engine failed to apply local registry storage IPsec policy on the computer |
| Windows |
5462 |
PAStore Engine failed to apply some rules of the active IPsec policy on the computer |
| Windows |
5463 |
PAStore Engine polled for changes to the active IPsec policy and detected no changes |
| Windows |
5464 |
PAStore Engine polled for changes to the active IPsec policy, detected changes, and applied them to IPsec Services |
| Windows |
5465 |
PAStore Engine received a control for forced reloading of IPsec policy and processed the control successfully |
| Windows |
5466 |
PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory cannot be reached, and will use the cached copy of the Active Directory IPsec policy instead |
| Windows |
5467 |
PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory can be reached, and found no changes to the policy |
| Windows |
5468 |
PAStore Engine polled for changes to the Active Directory IPsec policy, determined that Active Directory can be reached, found changes to the policy, and applied those changes |
| Windows |
5471 |
PAStore Engine loaded local storage IPsec policy on the computer |
| Windows |
5472 |
PAStore Engine failed to load local storage IPsec policy on the computer |
| Windows |
5473 |
PAStore Engine loaded directory storage IPsec policy on the computer |
| Windows |
5474 |
PAStore Engine failed to load directory storage IPsec policy on the computer |
| Windows |
5477 |
PAStore Engine failed to add quick mode filter |
| Windows |
5478 |
IPsec Services has started successfully |
| Windows |
5479 |
IPsec Services has been shut down successfully |
| Windows |
5480 |
IPsec Services failed to get the complete list of network interfaces on the computer |
| Windows |
5483 |
IPsec Services failed to initialize RPC server. IPsec Services could not be started |
| Windows |
5484 |
IPsec Services has experienced a critical failure and has been shut down |
| Windows |
5485 |
IPsec Services failed to process some IPsec filters on a plug-and-play event for network interfaces |
| Windows |
5632 |
A request was made to authenticate to a wireless network |
| Windows |
5633 |
A request was made to authenticate to a wired network |
| Windows |
5712 |
A Remote Procedure Call (RPC) was attempted |
| Windows |
5888 |
An object in the COM+ Catalog was modified |
| Windows |
5889 |
An object was deleted from the COM+ Catalog |
| Windows |
5890 |
An object was added to the COM+ Catalog |
| Windows |
6144 |
Security policy in the group policy objects has been applied successfully |
| Windows |
6145 |
One or more errors occured while processing security policy in the group policy objects |
| Windows |
6272 |
Network Policy Server granted access to a user |
| Windows |
6273 |
Network Policy Server denied access to a user |
| Windows |
6274 |
Network Policy Server discarded the request for a user |
| Windows |
6275 |
Network Policy Server discarded the accounting request for a user |
| Windows |
6276 |
Network Policy Server quarantined a user |
| Windows |
6277 |
Network Policy Server granted access to a user but put it on probation because the host did not meet the defined health policy |
| Windows |
6278 |
Network Policy Server granted full access to a user because the host met the defined health policy |
| Windows |
6279 |
Network Policy Server locked the user account due to repeated failed authentication attempts |
| Windows |
6280 |
Network Policy Server unlocked the user account |
| Windows |
6281 |
Code Integrity determined that the page hashes of an image file are not valid… |
| Windows |
6400 |
BranchCache: Received an incorrectly formatted response while discovering availability of content. |
| Windows |
6401 |
BranchCache: Received invalid data from a peer. Data discarded. |
| Windows |
6402 |
BranchCache: The message to the hosted cache offering it data is incorrectly formatted. |
| Windows |
6403 |
BranchCache: The hosted cache sent an incorrectly formatted response to the client’s message to offer it data. |
| Windows |
6404 |
BranchCache: Hosted cache could not be authenticated using the provisioned SSL certificate. |
| Windows |
6405 |
BranchCache: %2 instance(s) of event id %1 occurred. |
| Windows |
6406 |
%1 registered to Windows Firewall to control filtering for the following: |
| Windows |
6407 |
%1 |
| Windows |
6408 |
Registered product %1 failed and Windows Firewall is now controlling the filtering for %2. |
| Windows |
6409 |
BranchCache: A service connection point object could not be parsed |
| Windows |
6410 |
Code integrity determined that a file does not meet the security requirements to load into a process. This could be due to the use of shared sections or other issues |
| Windows |
6416 |
A new external device was recognized by the system. |
| Windows |
6417 |
The FIPS mode crypto selftests succeeded |
| Windows |
6418 |
The FIPS mode crypto selftests failed |
| Windows |
6419 |
A request was made to disable a device |
| Windows |
6420 |
A device was disabled |
| Windows |
6421 |
A request was made to enable a device |
| Windows |
6422 |
A device was enabled |
| Windows |
6423 |
The installation of this device is forbidden by system policy |
| Windows |
6424 |
The installation of this device was allowed, after having previously been forbidden by policy |
| Windows |
8191 |
Highest System-Defined Audit Message Value |
Event Log, Source EventID EventID Description
Pre-vista Post-Vista
Security, Security 512 4608 Windows NT is starting up.
Security, Security 513 4609 Windows is shutting down.
Security, USER32 --- 1074 The process nnn has initiated the restart of computer.
Security, Security 514 4610 An authentication package has been loaded by the Local Security Authority.
Security, Security 515 4611 A trusted logon process has registered with the Local Security Authority.
Security, Security 516 4612 Internal resources allocated for the queuing of audit messages
have been exhausted, leading to the loss of some audits.
Security, Security 518 4614 A notification package has been loaded by the Security Account Manager.
Security, Security, 519 4615 A process is using an invalid local procedure call (LPC) port.
Security, Security 520 4616 The system time was changed.
Security, Security 521 --- Unable to log events to security log.
Security, Security(Logon/Logoff) 528 4624 Successful Logon.
Security, Security(Logon/Logoff) 540 4624 Successful Network Logon.
Security, Security(Logon/Logoff) 529 4625 Logon Failure - Unknown user name or bad password.
Security, Security(Logon/Logoff) 530 4625 Logon Failure - Account logon time restriction violation.
Security, Security(Logon/Logoff) 531 4625 Logon Failure - Account currently disabled.
Security, Security(Logon/Logoff) 532 4625 Logon Failure - The specified user account has expired.
Security, Security(Logon/Logoff) 533 4625 Logon Failure - User not allowed to logon at this computer.
Security, Security(Logon/Logoff) 534 4625 Logon Failure - The user has not been granted the requested logon type
at this machine.
Security, Security(Logon/Logoff) 535 4625 Logon Failure - The specified account's password has expired.
Security, Security(Logon/Logoff) 536 4625 Logon Failure - The NetLogon component is not active.
Security, Security(Logon/Logoff) 537 4625 Logon failure - The logon attempt failed for other reasons.
Security, Security(Logon/Logoff) 538 4634 User Logoff.
Security, Security(Logon/Logoff) 539 4625 Logon Failure - Account locked out.
Security, Security(Logon/Logoff) --- 4646 IKE DoS-prevention mode started.
Security, Security(Logon/Logoff) 551 4647 User initiated logoff.
Security, Security(Logon/Logoff) 552 4648 A logon was attempted using explicit credentials.
Security, Security(Logon/Logoff) 553 4649 A replay attack was detected.
Security, Security(Logon/Logoff) 601 4697 A service was installed in the system.
Security, Object access --- 4688 A new process created.
Security, Object access --- 4697 A new service installed.
Security, Object access 602 4698 A scheduled task was created.
Security, Object access 602 4699 A scheduled task was deleted.
Security, Object access 602 4700 A scheduled task was enabled.
Security, Object access 602 4701 A scheduled task was disabled.
Security, Object access 602 4702 A scheduled task was updated.
Security, Account Management 624 4720 User Account Created.
Security, Account Management 626 4722 User Account Enabled.
Security, Account Management 627 4723 Change Password Attempt.
Security, Account Management 628 4724 User Account password set.
Security, Account Management 629 4725 User Account Disabled.
Security, Account Management 630 4726 User Account Deleted.
Security, Account Management 636 4732 Local User Account Created.
Security, Account Management 642 4738 User Account Changed.
Security, Account Management 643 4739 GPO changed.
Security, Account Management 644 4740 User Account Locked Out.
Security, Account Management 645 4741 Computer Account Created.
Security, Account Management 646 4742 Computer Account Changed.
Security, Account Management 647 4743 Computer Account Deleted.
Security, Account Management 671 4767 A user account was unlocked.
Security, Security(Logon/Logoff) --- 4768 Kerberos TGT was requested.
Security, Security(Logon/Logoff) --- 4771 Kerberos pre-authentication failed.
Security, Security(Logon/Logoff) --- 4772 Kerberos TGT request failed.
Security, Security(Logon/Logoff) 678 4774 An account was mapped for logon.
Security, Security(Logon/Logoff) 679 4775 The name: %2 could not be mapped for logon by: %1
Security, Security(Logon/Logoff) 680 4776 Account Used for Logon by.
Security, Security(Logon/Logoff) 681 4777 The logon to account: %2 by: %1 from workstation: %3 failed.
Security, Security(Logon/Logoff) 682 4778 Session reconnected to winstation.
Security, Security(Logon/Logoff) 683 4779 Session disconnected from winstation.
Security, Security(Logon/Logoff) --- 4800 The workstation was locked.
Security, Security(Logon/Logoff) --- 4801 The workstation was unlocked.
Security, Security(Logon/Logoff) --- 4802 The screen saver was invoked.
Security, Security(Logon/Logoff) --- 4803 The screen saver was dismissed.
Security, Account Management --- 5136 GPO changed.
Security, Account Management --- 5137 GPO created.
Security, Account Management --- 5141 GPO deleted.
System, EventLog, 6005 6005 The event log was started.
System, EventLog, 6006 6006 The Event log service was stopped.
System, EventLog, 6013 6013 System uptime.
System, EventLog, 517 1102 The audit log was cleared.
System, EventLog, --- 1104 The security Log is now full.
System, EventLog, --- 1105 Event log automatic backup.
System, EventLog, --- 1108 The event logging service encountered an error.
System, Service Control Manager 7035 7035 The nnn service was successfully sent a start/Stop control.
System, Service Control Manager 7036 7036 The nnn service entered the Running/Stopped state.
System, W32Time, 29 29 The time provider NtpClient is configured to acquire time from
one or more time sources; however none of the sources are currently accessible.
System, W32Time, 38 38 The time provider NtpClient cannot reach or is currently receiving invalid time data.
System, W32Time, 47 47 Time Provider NtpClient: No valid response received.
External media detection -- 43 new device information.
External media detection -- 400 new mass storage installation.
Software and service installation -- 903,903 new application installation.
Software and service installation -- 905,906 updated application.
Software and service installation -- 907,908 removed application.
Software and service installation -- 1022,1033 new MSI file installed.
Software and service installation -- 6 new kernel filter driver.
AD/Server groups Event IDs:
| GROUP CHANGES | CREATED | CHANGED | DELETED | MEMBERS | ||
|---|---|---|---|---|---|---|
| ADDED | REMOVED | |||||
| SECURITY | Local | 4731 | 4737 | 4734 | 4732 | 4733 |
| Global | 4727 | 4735 | 4730 | 4728 | 4729 | |
| Universal | 4754 | 4755 | 4758 | 4756 | 4757 | |
| DISTRIBUTION | Local | 4744 | 4745 | 4748 | 4746 | 4747 |
| Global | 4749 | 4750 | 4753 | 4751 | 4752 | |
| Universal | 4759 | 4760 | 4763 | 4761 | 4762 |
All logon/logoff events include a Logon Type code, the precise type of logon or logoff: 2 Interactive 3 Network (remote file shares / printers/iis) 4 Batch (scheduled task) 5 Service (service account) 7 Unlock 8 NetworkCleartext (IIS) 9 NewCredentials (RunAs /netonly) 10 RemoteInteractive (Terminal Services,RDP) 11 CachedInteractive (cached credentials) When working with Event IDs it can be important to specify the source in addition to the ID, the same number can have different meanings in different logs from different sources.
So, that’s all in this blog. I will meet you soon with some other stuff. Have a nice day !!!
Recommended content
RODC Installation Guide- Step by step guide to install read only domain controller
RODC Filtered Attribute Set
Installing and configuring a RODC in Windows Server-2012
How to find the GUID of Domain Controller
Group Policy Understanding Group Policy Preferences
Group Policy Verification Tool GPOTool Exe
Group Policy Health Check on Specific Domain Controller
What is Netlogon Folder in Active Directory
How to Create Custom Attributes in Active Directory
How Can I Check the Tombstone Lifetime of My Active Directory Forest
How to Determine a Computers AD Site From the Command Line
How to Check the Active Directory Database Integrity
How to Check the Active Directory Database Integrity
Disabling and Enabling the Outbound Replication
DFS Replication Service Stopped Replication
What is Strict Replication Consistency
The replication operation failed because of a schema mismatch between the servers involved
Troubleshooting ad replication error 8418 the replication operation failed because of a schema mismatch between the servers
How to export replication information in txt file
Repadmin Replsummary
Enabling the outbound replication
Guys please don’t forget to like and share the post.Also join our WindowsTechno Community and where you can post your queries/doubts and our experts will address them .
You can also share the feedback on below windows techno email id.
If you have any questions feel free to contact us on admin@windowstechno.com also follow us on facebook@windowstechno to get updates about new blog posts.
Was this article helpful?
YesNo
He is an Active Directory Engineer. He has been working in IT industry for more than 10 years. He is dedicated and enthusiastic information technology expert who always ready to resolve any technical problem. If you guys need any further help on subject matters, feel free to contact us on admin@windowstechno.com Please subscribe our Facebook page as well website for latest article. https://www.facebook.com/windowstechno
Журнал событий Windows (Event Log) — это важный инструмент, который позволяет администратору отслеживать ошибки, предупреждения и другие информационные сообщения, которые регистрируются операционной системой, ее компонентами и различными программами. Для просмотра журнала событий Windows можно использовать графическую MMC оснастку Event Viewer (
eventvwr.msc
). В некоторых случаях для поиска информации в журналах событий и их анализа гораздо удобнее использовать PowerShell. В этой статье мы покажем, как получать информацию из журналов событий Windows с помощью командлета Get-WinEvent.
Содержание:
- Получение логов Windows с помощью Get-WinEvent
- Get-WinEvent: быстрый поиск в событиях Event Viewer с помощью FilterHashtable
- Расширенный фильтры событий Get-WinEvent с помощью FilterXml
- Получить логи Event Viewer с удаленных компьютеров
На данный момент в Windows доступны два командлета для доступа к событиям в Event Log: Get-EventLog и Get-WinEvent. В подавляющем большинстве случаев рекомендуем использовать именно Get-WinEvent, т.к. он более производителен, особенно в сценариях обработки большого количества событий с удаленных компьютеров. Командлет Get-EventLog является устаревшим и использовался для получения логов в более ранних версиях Windows. Кроме того, Get-EventLog не поддерживается в современных версиях PowerShell Core 7.x.
Получение логов Windows с помощью Get-WinEvent
Для использования команды Get-WinEvent нужно запустить PowerShell с правами администратора (при запуске Get-WinEvent от имени пользователя вы не сможете получить доступ к некоторым логам, например, к Security).
Для получения списка событий из определенного журнала, нужно указать его имя. В данном примере мы выведем последние 20 событий из журнала System:
Get-WinEvent -LogName Application -MaxEvents 20
Чаще всего вам нужно будет получать информацию из журналов System, Application, Security или Setup. Но вы можете указать и другие журналы. Полный список журналов событий в Windows можно получить с помощью команды:
Get-WinEvent -ListLog *
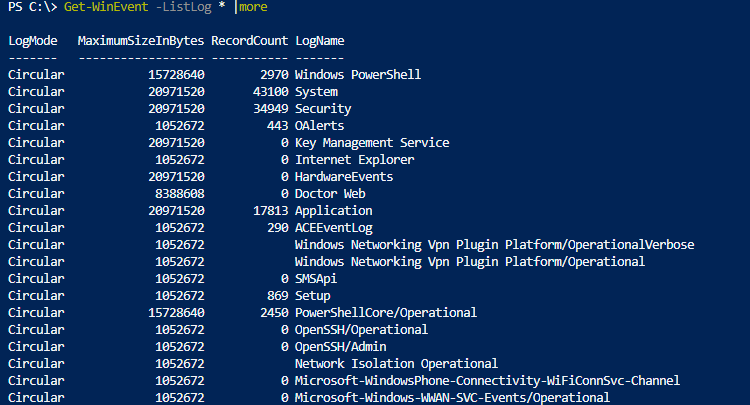
Например, чтобы вывести события RDP подключений к компьютеру, нужно указать лог Microsoft-Windows-TerminalServices-RemoteConnectionManager/Operational:
Get-WinEvent -LogName Microsoft-Windows-TerminalServices-RemoteConnectionManager/Operational
Или получить логи SSH подключений к Windows из журнала OpenSSH/Operational:
Get-WinEvent -LogName OpenSSH/Operational
Можно выбрать события сразу из нескольких журналов. Например, чтобы получить информацию о ошибках и предупреждениях из журналов System и Application за последние 24 часа (сутки), можно использовать такой код:
$StartDate = (Get-Date) - (New-TimeSpan -Day 1)
Get-WinEvent Application,System | Where-Object {($_.LevelDisplayName -eq "Error" -or $_.LevelDisplayName -eq "Warning") -and ($_.TimeCreated -ge $StartDate )}
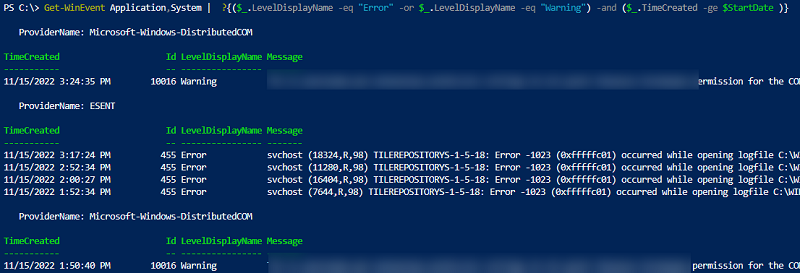
Чтобы вывести только определенные поля событий, можно использовать Select-Object или Format-Table:
Get-WinEvent -LogName System | Format-Table Machinename, TimeCreated, Id, UserID
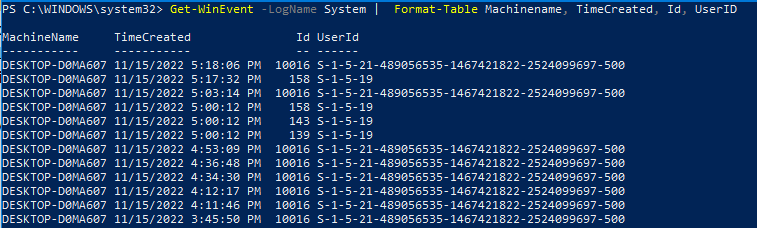
Можно выполнить дополнительные преобразования с полученными данными. Например, в этом примере мы сразу преобразуем имя пользователя в SID:
Get-WinEvent -filterhash @{Logname = 'system'} |
Select-Object @{Name="Computername";Expression = {$_.machinename}},@{Name="UserName";Expression = {$_.UserId.translate([System.Security.Principal.NTAccount]).value}}, TimeCreated
Get-WinEvent: быстрый поиск в событиях Event Viewer с помощью FilterHashtable
Рассмотренный выше способ выбора определенных событий из журналов Event Viewer с помощью Select-Object прост для понимая, но выполняется крайне медленно. Это особенно заметно при выборке большого количества событий. В большинстве случаев для выборки событий нужно использовать фильтрацию на стороне службы Event Viewer с помощью параметра FilterHashtable.
Попробуем сформировать список ошибок и предупреждений за 30 дней с помощью Where-Object и FilterHashtable. Сравнима скорость выполнения этих двух команд PowerShell с помощью Measure-Command:
$StartDate = (Get-Date).AddDays(-30)
Проверим скорость выполнения команды с Where-Object:
(Measure-Command {Get-WinEvent Application,System | Where-Object {($_.LevelDisplayName -eq "Error" -or $_.LevelDisplayName -eq "Warning") -and ($_.TimeCreated -ge $StartDate )}}).TotalMilliseconds
Аналогичная команда с FilterHashtable:
(Measure-Command {Get-WinEvent -FilterHashtable @{LogName = 'System','Application'; Level =2,3; StartTime=$StartDate }})..TotalMilliseconds
В данном примере видно, что команда выборки событий через FilterHashtable выполняется в 30 раз быстрее, чем если бы обычный Where-Object (
2.5
сек vs
76
секунд).
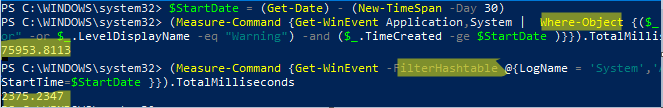
Если вам нужно найти события по EventID, используйте следующую команду с FilterHashtable:
Get-WinEvent -FilterHashtable @{logname='System';id=1074}|ft TimeCreated,Id,Message
В параметре FilterHashtable можно использовать фильтры по следующим атрибутам событий:
- LogName
- ProviderName
- Path
- Keywords (для поиска успешных событий нужно использовать значение 9007199254740992 или для неуспешных попыток 4503599627370496)
- ID
- Level (1=FATAL, 2=ERROR, 3=Warning, 4=Information, 5=DEBUG, 6=TRACE, 0=Info)
- StartTime
- EndTime
- UserID (SID пользователя)
- Data
Пример поиска события за определенный промежуток времени:
Get-WinEvent -FilterHashTable @{LogName='System'; StartTime=(get-date).AddDays(-7); EndTime=(get-date).AddHours(-1); ID=1234}
Если нужно найти определенный текст в описании события, можно использовать такую команду:
Get-WinEvent -FilterHashtable @{logname='System'}|Where {$_.Message -like "*USB*"}
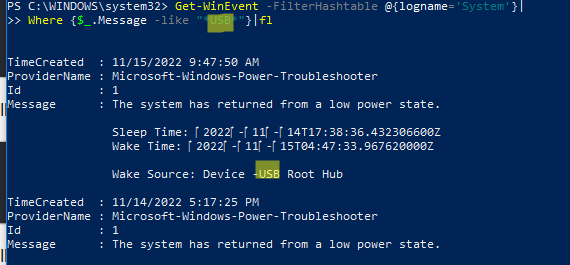
Расширенный фильтры событий Get-WinEvent с помощью FilterXml
Фильтры Get-WinEvent с параметром FilterHashtable являются несколько ограниченными. Если вам нужно использовать для выборки событий сложные запросы с множеством условий, нужно использовать параметр FilterXml, который позволяет сформировать запрос на выбор событий в Event Viewer с помощью XML запроса. Как и FilterHashtable, фильтры FilterXml выполняется на стороне сервера, поэтому результат вы получите довольно быстро.
Например, аналогичный запрос для получения последних ошибок из журнала System за последние 30 дней может выглядеть так:
$xmlQuery = @'
<QueryList>
<Query Id="0" Path="System">
<Select Path="System">*[System[(Level=2 or Level=3) and TimeCreated[timediff(@SystemTime) <= 2592000000]]]</Select>
</Query>
</QueryList>
'@
Get-WinEvent -FilterXML $xmlQuery
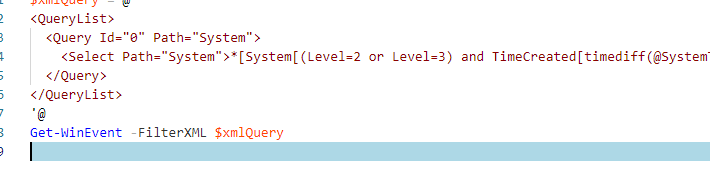
Для построения кода сложных XML запросов можно использовать графическую консоль Event Viewer:
- Запустите
eventvwr.msc
; - Найдите журнал для которого вы хотите создать и выберите Filter Current Log;
- Выберите необходимые параметры запроса в форме. В этом примере я хочу найти события с определенными EventID за последние 7 дней от определенного пользователя;
- Чтобы получить код XML запроса для параметра FilterXML, перейдите на вкладку XML и скопируйте полученный код (CTRL+A, CTRL+C);
- Если нужно, вы можете вручную отредактировать данный запрос.
Для экспорта списка событий в CSV файл нужно использовать командлет Export-CSV:
$Events= Get-WinEvent -FilterXML $xmlQuery
$events| Export-CSV "C:\ps\FilterSYSEvents.csv" -NoTypeInformation -Encoding UTF8
Получить логи Event Viewer с удаленных компьютеров
Для получения события с удаленного компьютер достаточно указать его имя в параметре -ComputerName:
$computer='msk-dc01'
Get-WinEvent -ComputerName $computer -FilterHashtable @{LogName="System"; StartTime=(get-date).AddHours(-24)} | select Message,Id,TimeCreated
Можно опросить сразу несколько серверов/компьютеров и поискать на них определенные события. Список серверов можно получить из текстового файла:
$servers = Get-Content -Path C:\ps\servers.txt
Или из Active Directory:
$servers = (Get-ADComputer -Filter 'operatingsystem -like "*Windows server*" -and enabled -eq "true"').Name
foreach ($server in $servers) {
Get-WinEvent -ComputerName $server -MaxEvents 5 -FilterHashtable @{
LogName = 'System'; ID= 1234
} | Select-Object -Property ID, MachineName
}
Здесь есть другой пример для поиска событий блокировки учетной записи пользователя на всех контроллерах домена:
$Username = 'a.ivanov'
Get-ADDomainController -fi * | select -exp hostname | % {
$GweParams = @{
‘Computername’ = $_
‘LogName’ = ‘Security’
‘FilterXPath’ = "*[System[EventID=4740] and EventData[Data[@Name='TargetUserName']='$Username']]"
}
$Events = Get-WinEvent @GweParams
$Events | foreach {$_.Computer + " " +$_.Properties[1].value + ' ' + $_.TimeCreated}
}